The Internet of Things (IoT) enables the power of the Internet and analytics to be given to the real world of physical objects. In IoT world, a physical object needs to be connected to the Internet using a connectivity method to send its data in order to be processed in real time or offline. This data could be used to control the object itself or control the other objects in a smarter manner. Therefore, we can look at the IoT as a network of connected objects which are able to exchange data and information via the Internet. Years ago, the idea of establishing a network of massive physical objects seemed impossible or at least impractical. The fact that a physical object needs to have a processor and a means to connect to other physical objects would impose challenges that made the widespread use of IoT impractical.
There is a broad range of physical objects that fall under that umbrella of connected Things. A Thing can be as simple as a temperature sensor that gathers the temperature data to monitor the temperature inside a building. An appliance can be considered as a Thing in which it can exchange data through the Internet with other objects that assist the appliance to manage its energy consumption more effectively, improve its performance, or increase safety of its operation.
Since the Things are connected to the Internet, they can send their data to a data center or cloud for processing. For most applications, the duration of sending data from the physical object to a remote data center, or even the round-trip time for transmitting the data to the cloud, processing and analyzing the data, and sending information back to the object is not too large to cause any problem. In situations that the delay is too large, edge-computing can be used. In edge computing, an edge device within relatively close distance to the physical objects can process the data, and send the information to the physical objects to reduce the delay. An edge device can also aggregate the data before sending it for further processing or storage.
Coca-Cola vending machine at Carnegie Mellon University might be considered as the first device that brought to light the concept of a network with smart devices. This vending machine could report its inventory remotely in 1982 before the era of modern Internet. Therefore, we may not name it as Internet of Things, but certainly was a network of things. A toaster that could be turned on and off remotely over the Internet was introduced in 1990 and can be considered as one of the first IoT devices. But, the term “Internet of Things” was coined by Kevin Ashton, to promote Radio Frequency Identification (RFID) technology in 1999. He used this term as a buzz word to get the attention of the management to RFID technology. The IoT concept did not gain much of popularity until 2010. Gartner added the name IoT on its “hype-cycle for emerging technologies” in 2011. Nowadays, IoT technology has made itself well established across many industries such as healthcare, energy and industrial automation. The use cases of IoT are increasing at a very fast pace. The number of IoT devices deployed is expected to grow exponentially, and we can expect increasing amount of data exchange through the Internet by the physical objects.
IoT is going to change every aspect of our life. The IoT chip designers and manufacturers are investing heavily in IoT technology. The number of IoT chip manufactures and IoT modules have been increased substantially during past years. The number of production of IoT modules are also increasing rapidly. These IoT modules, nowadays are part of different devices used by a variety of industries. The list of the industries that are using IoT is growing rapidly as well. Transportation, energy, smart cities, retail, agriculture, and healthcare are some examples of industries that utilize IoT technology.
IoT is changing telecommunication industry which provides connectivity for IoT. Telecommunication companies and service providers are trying to accommodate with the requirements needed by IoT. Due to its unique characteristics, IoT brings many changes to service providers. However, this is not new for telecommunication companies. Many years ago, telecommunication companies provided only voice services to their costumers. The need for data services introduced a substantial change in structure of these companies where they were able to successfully accommodate the new requirements and manage the needed modifications to their network. IoT has its own characteristics that are unique and somehow different than voice and data services already provided by service providers to people. The IoT devices usually need higher uplink bandwidth as compared to downlink, while humans generate more downlink traffic. The traffic generated by an IoT device can be significantly lower or higher as compared to the traffic generated by a person. For example, a metering device might need to transmit only several bytes per day, while an industrial machine installed in a smart factory might need to transmit several kilobytes of data per second. In most applications, the IoT device sends its data through the day periodically, while the people generate more traffic during the day as compared to the night time. Also, in some IoT applications, the IoT device sends its data after an event is detected, while the traffic generated by humans is not usually event based.
Since the huge amount of data produced by a staggering number of IoT devices needs to be stored, processed, and analyzed, IoT will continue to make new opportunities for cloud providers, application designers, data analyzers, and system integrators as more and more organizations realize the true power of IoT.
IoT can be categorized into three different clusters of verticals, use cases and applications, in which each vertical has several use cases and each use case can have several applications. IoT vertical indicates the use of IoT in a specific industry segment. An IoT vertical has unique regulatory bodies, supports specific standards, policies, procedures and protocols. Each vertical can be further divided into use cases. A use case usually is served by the same platform and they usually need similar methodology for processing, storing, and analyzing the data. For example, in the transportation vertical, there may be use cases related to autonomous vehicles. Each use case may include several applications. Applications often use similar solutions and software programs. Sometimes the IoT vertical is divided into sub verticals to make a four layer categorization. Unfortunately, the above mentioned taxonomy is not used in practice and there is no common agreement on IoT categorization. For example, you may find manufacturing as an IoT vertical in some documents, while it has been considered as a use case under industrial vertical in other places. The need for categorization comes from the fact that two similar applications, belonging to different use cases or even different verticals might be quite different due to their requirements in terms of regulatory bodies, standards, policies, protocols, platforms, processing and etc.
IoT can be implemented using many IoT connectivity schemes that connect an IoT device to the other devices through the Internet. In general, the Internet connection can be either wired, or wireless. Wired and wireless communications have their own advantages and disadvantages and should be chosen depending on the application. Understanding the benefits and drawbacks of wired and wireless connectivity schemes enables us to make an informed decision regarding IoT implementing solution. There are many factors that affect this selection. Example of these factors are the number of IoT nodes in the network, the location of nodes, the maximum range of the network, the required bandwidth or data rate, the maximum power consumption allowed, and the security requirements.
Wired connections are reliable, fast and very secure. They are more reliable than wireless connections since they are less prone to packet loss as a result of path loss or interferences from other electronic devices. However, they suffer from higher cost of implementation, and lack of support for mobility. Scalability is also another problem with wired networks. The wired IoT network is only practical if IoT devices not only are close to each other to reduce the cabling cost, but also at least one of them is located close enough to a wired Internet access point. For many IoT applications, wired connectivity is not very practical and wireless IoT implementations are the common solutions.
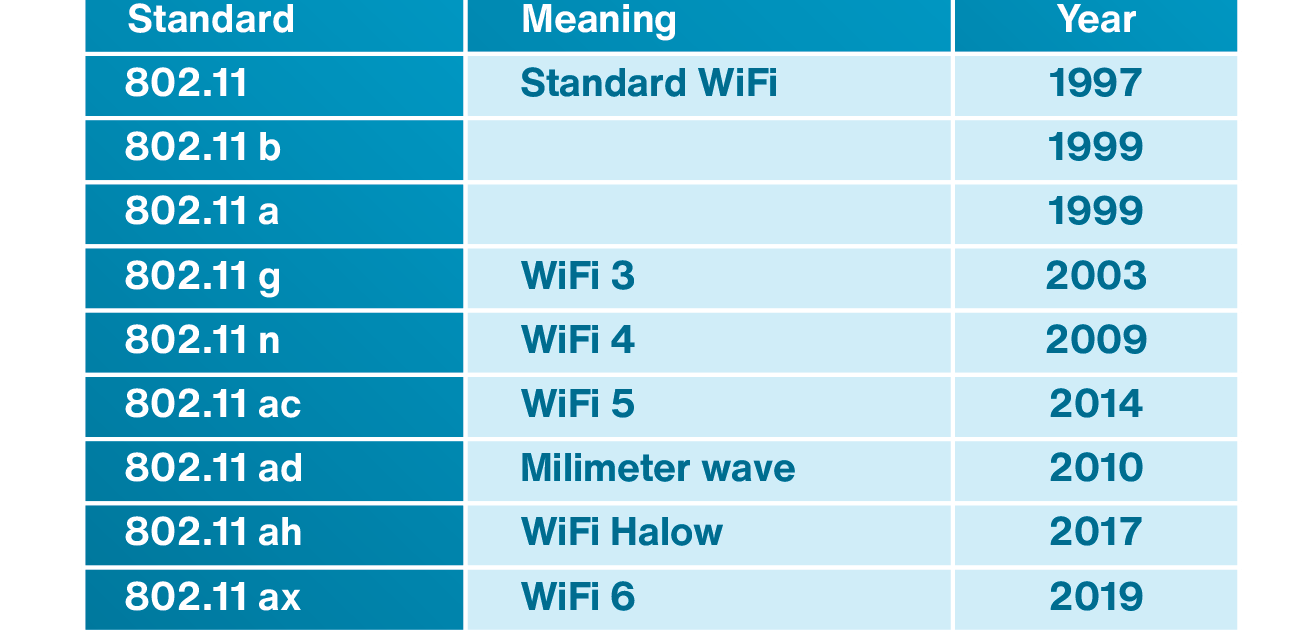
Short-range wireless technologies such Bluetooth, Zigbee or even WiFi are enablers of IoT. These technologies use the Industrial, Science, and Medicine (ISM) spectrum which make them very attractive. To connect the IoT devices to the Internet using these technologies, there is a need for an IoT gateway which on one hand is connected to the IoT physical device using short-range technologies and on the other hand is connected to the Internet. The IoT gateway is located at the edge of the local network, and sometimes has enough processing power to perform some computing at the edge. Figure 1.1 shows a situation that many IoT devices are connected to an IoT gateway to send their data to the Internet.

Figure 1.1: IoT gateway for the Internet connection
Wireless IoT is becoming a mature technology, expanding rapidly into more and more industries, and is creating a domain of devices that in many situations are battery operated. In many applications, it would be extremely challenging to replace these batteries. For this reason, low power consumption is one of the requirement of wireless IoT technology. Another reason for designing IoT devices with low power consumption comes from the fact that there will be a massive number of IoT devices in the future. If we can reduce the power consumption of each device, we consequently need less energy to be produced to power up these devices. While there are different sources of energy such as wind, and solar that are renewable and some what are clean, most of the energy generated today comes from burning fuel. To reduce the power consumption of the IoT devices, the device needs to go to sleep if it does not have anything to perform. The longer the device sleeps, the lower amount of energy is consumed which increases the life time of the battery. Since low power consumption is one of the most important characteristics of wireless IoT, technologies such as Bluetooth Low Energy (BLE) or Zigbee are often used in IoT applications. WiFi might be used in IoT applications that require higher bandwidth and the ones that power consumption is not a concern.
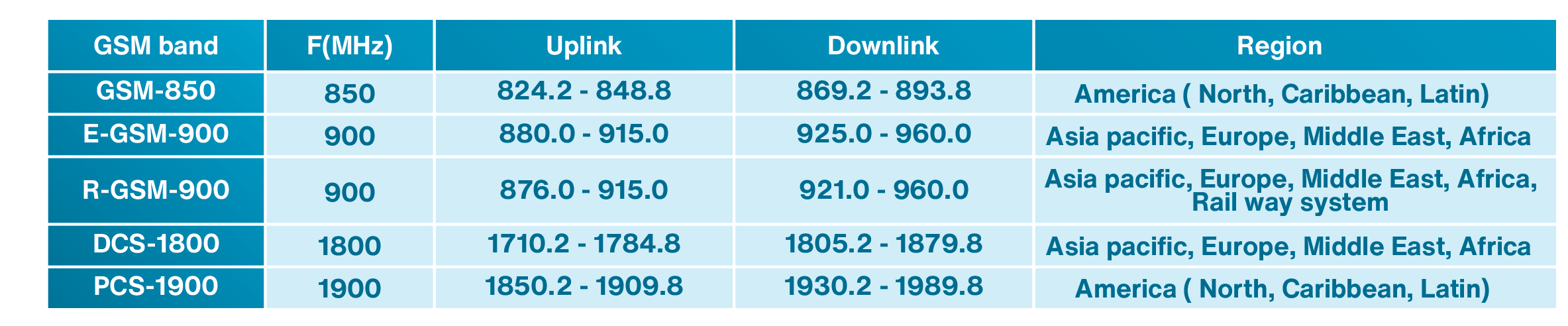
Besides short-range technologies that connect the IoT device to the Internet through gateway, there is another option that is particularly designed for providing long-range connectivity. A Low-Power Wide-Area Network (LPWAN) is a cellular network that provides long-range connectivity for devices that require low power consumption. The Cellular IoT (CIOT) networks have high reliability as well as availability and provide a good coverage. The CIoT technology can be divided into licenced and un-licenced technologies. The licenced-band IoT technology has superior performance in terms of expandability, interoperability, security, coverage, and Quality of Service (QoS). The most important unlicensed cellular technologies are Sigfox and Long Range Radio (LoRa).
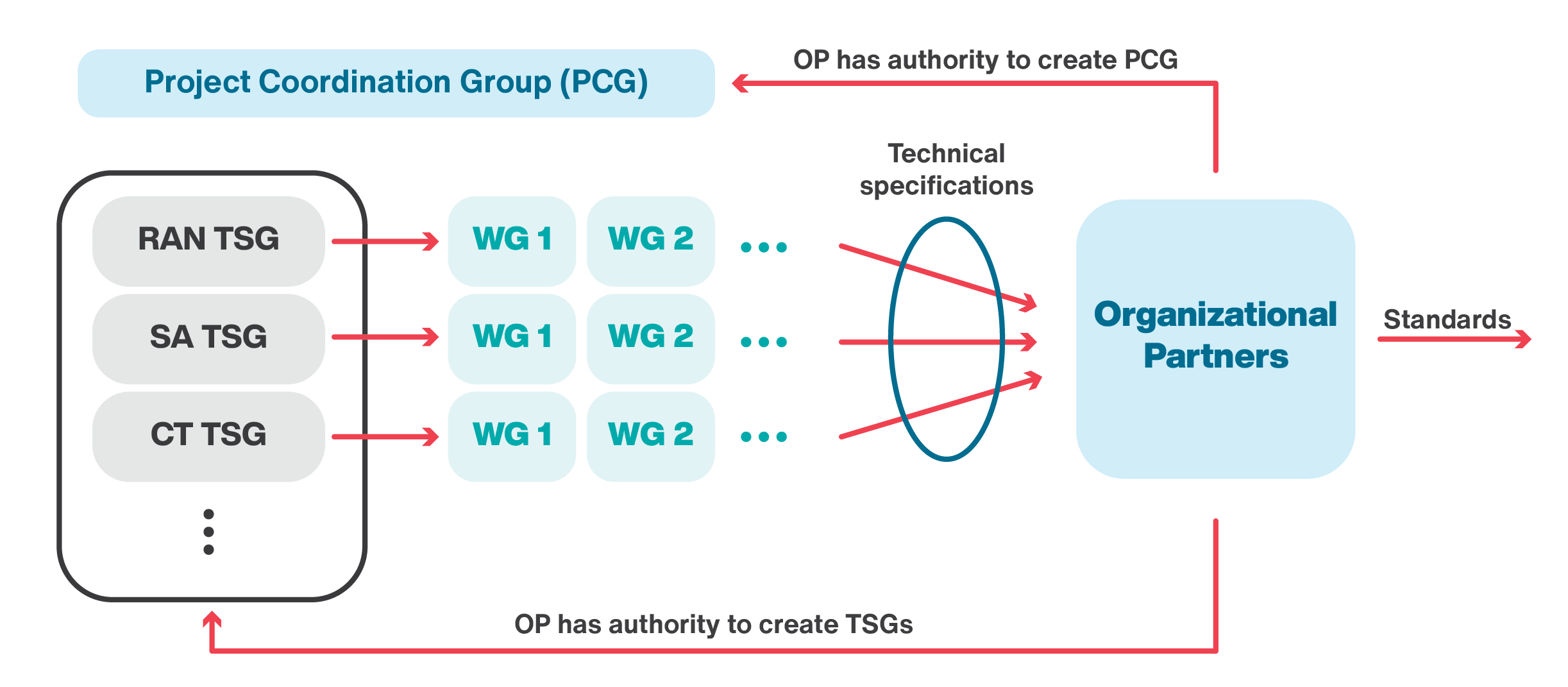
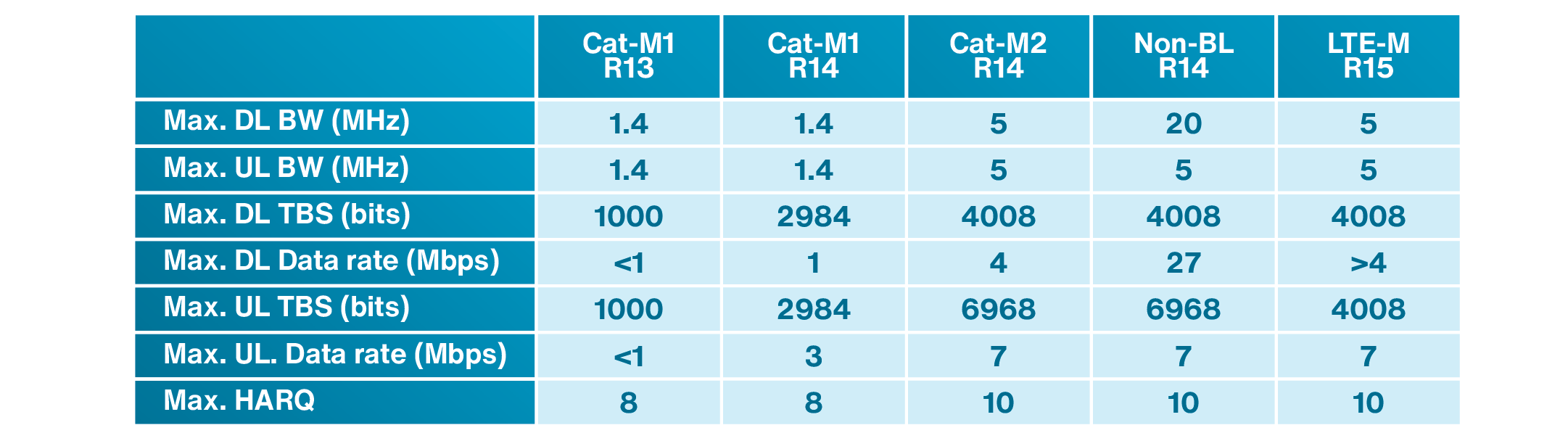
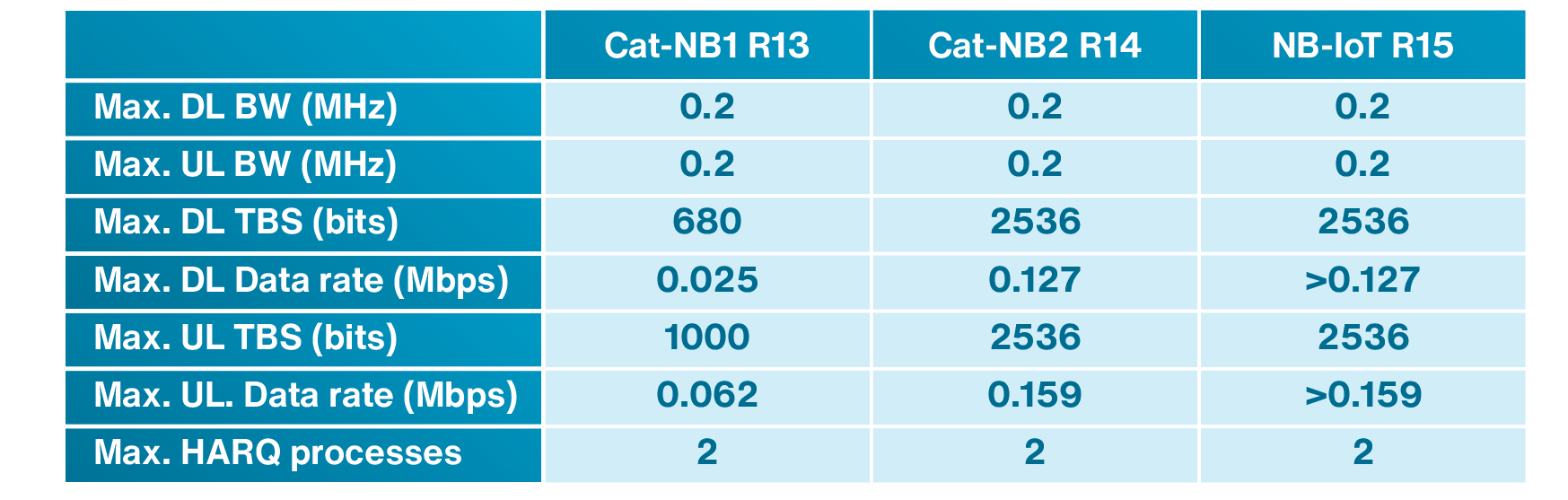
The Third Generation Partnership Project (3GPP) is the global technical body which develops technical specifications for mobile communication systems. The 3GPP cellular IoT technologies belong to the category of LPWAN systems. The licenced-band CIoT has been implemented using different generations of cellular network. Many IoT applications can be implemented using existing second (2G), third (3G), and fourth (4G) generations of cellular technologies. Fourth generation of cellular network has made it possible to achieve larger bandwidth, lower latency and greater density. Cellular IoT can be enhanced substantially in terms of capacity, coverage, density per cell, latency, and power consumption by using fifth generation of cellular networks (5G). 3GPP has developed technical specifications in its Release 13, 14 and 15 for IoT applications using 2G, 3G, and 4G cellular technologies. 5G cellular network has been designed for three different types of applications. The first one is mobile broadband (cellphones). The second one is massive machine type communications (MTC). This category is designed specifically for IoT applications. The last one is ultra reliable and low latency communications which is made and tailored especially to be suitable for real time and safety applications. Therefore, 5G cellular network addresses the needs and requirements of IoT applications as part of its design.
IoT provides precise insights to many applications in different sectors of a variety of industries and businesses. It brings efficiency, safety and can revolutionize the way many businesses and industries operate. For instance, energy companies in the field of oil and gas have their operations spread across many remote locations. IoT technology can provide these companies with continuous monitoring of their remote sites. Manufacturing relies heavily on complex machineries to manufacture products. Therefore, manufacturers have an interest in improving the performance of these machines. Connecting the machines to the Internet can improve precision, increase safety and bring efficiency to the operation of these machines. In this section, we will discuss some use cases of IoT to give the readers some understanding of how IoT brings changes to various industries.
1.3.1 IoT for Research
Scientists, researchers, and conservationists study the behavior of animals and try to understand the factors that are important to their survival. The natural habitat of many animals is under threat due to factors such as climate change, or disruption in food chain. The population of many species are shrinking, and many are becoming extinct. To save these species, there is a need to find out everything about their behavior and living. Understanding the animals’ travel habits and trajectories, or the locations that they search for food, are examples of important information that can help the scientists to save these endangered animals.
The data related to animal behavior can be obtained using IoT technology and through tagging the animals with sensors. A wearable IoT can be attached to the animal’s body to sense parameters such as location, temperature, and type of activities. The collected data can be stored in a database and used by the scientists to identify the important factors that can address the animal’s behavior. Scientists can use the data to design scientific models that can be used to protect endangered or threatened species. There are thousands of animals that are listed as endangered. Using the collected data, the scientists can better understand why the population is in decline and what solid actions need to be taken to help them survive. Figure 1.2 shows examples of using IoT to establish connected habitats for understanding the animals’ behavior by tracking their location, monitoring their heath signals, or generating event-based images or establishing connected habitats.
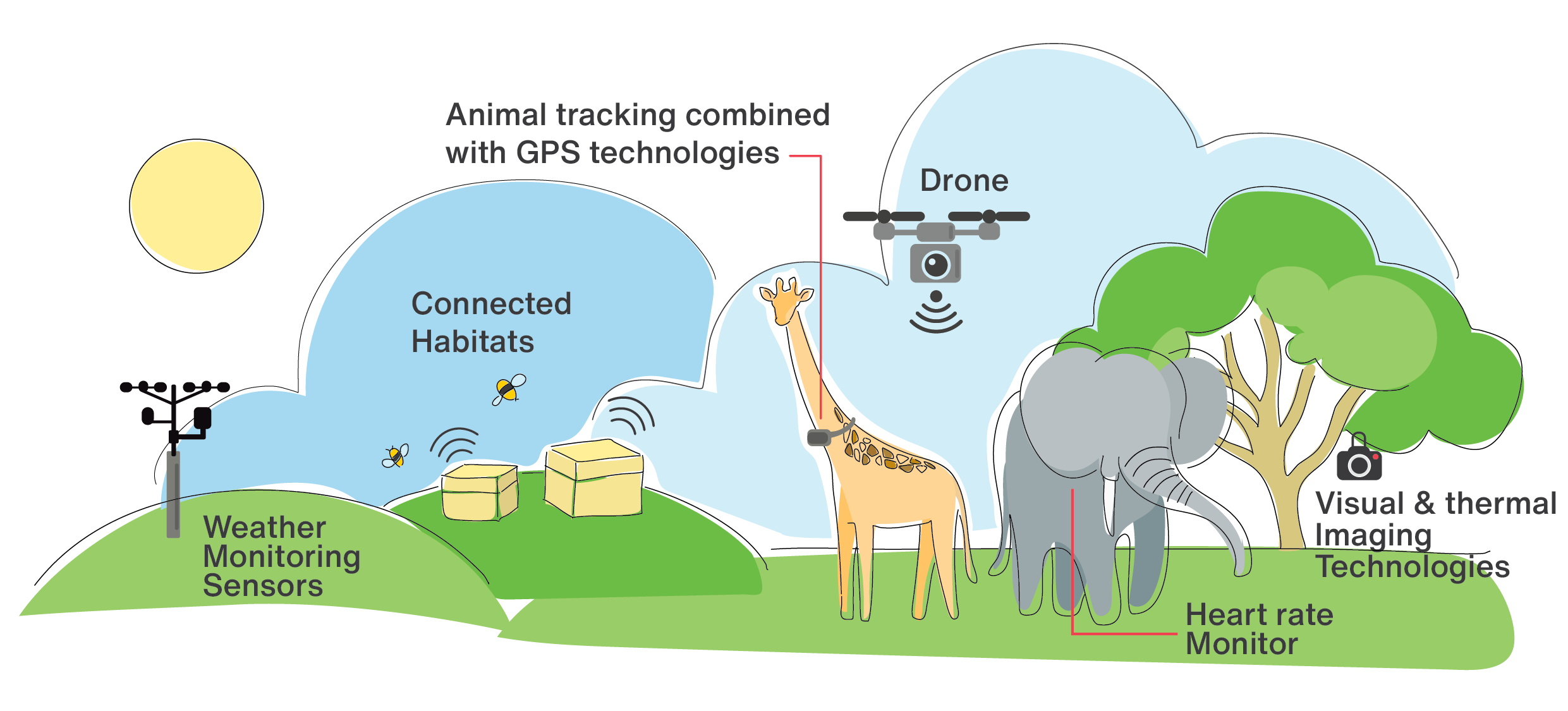 Figure 1.2: Use of IoT technology for research purposes on animal behavior
Figure 1.2: Use of IoT technology for research purposes on animal behavior
Cellular IoT technologies are designed to connect massive number of devices that can be spread over large geographical areas together. These technologies also try to be low in power consumption in such a way that battery operated devices can work for a long time before there is a need for battery replacement. Hence, wearable IoT devices can be used to monitor animals’ life and behavior over a long period of time and in large geographical areas. Considering around 50 bytes of data in both uplink and downlink direction every two hours, a typical CIoT device equipped with a Lithium coin cell battery (with 660 mWh capacity) can work for up to 2 years without using any harvesting technique to charge the battery. Obviously, if the rate of data transmission is lower, the battery can last longer. For example, by sending 50 bytes of data every day, the battery can last for more than 30 years.
1.3.2 Connected Street Lighting poles
In the past, the main reason for street lighting poles in urban areas was to provide visibility or safety. However, connecting these infrastructures to the Internet can provide a wide range of applications and opportunities and can be considered as a foundation for a smart city. Once the lighting systems and light poles are connected to the Internet, they can be used as the infrastructure for many smart city initiatives. For example, imaging sensors such as video surveillance cameras can be installed on the lighting poles for public safety purposes. Installing environmental monitoring sensors that can detect the air quality, or noise level can also be another example of sensors to change these infrastructures as environmental monitoring stations. Connected lighting poles can also be used as Wi-Fi access points which can consequently provide Internet access for some close by systems such as parking meters or pay stations. Connected light poles can be suitable locations to install street name signage or display systems to provide real-time information such as traffic to drivers, cyclists, pedestrians and residents.
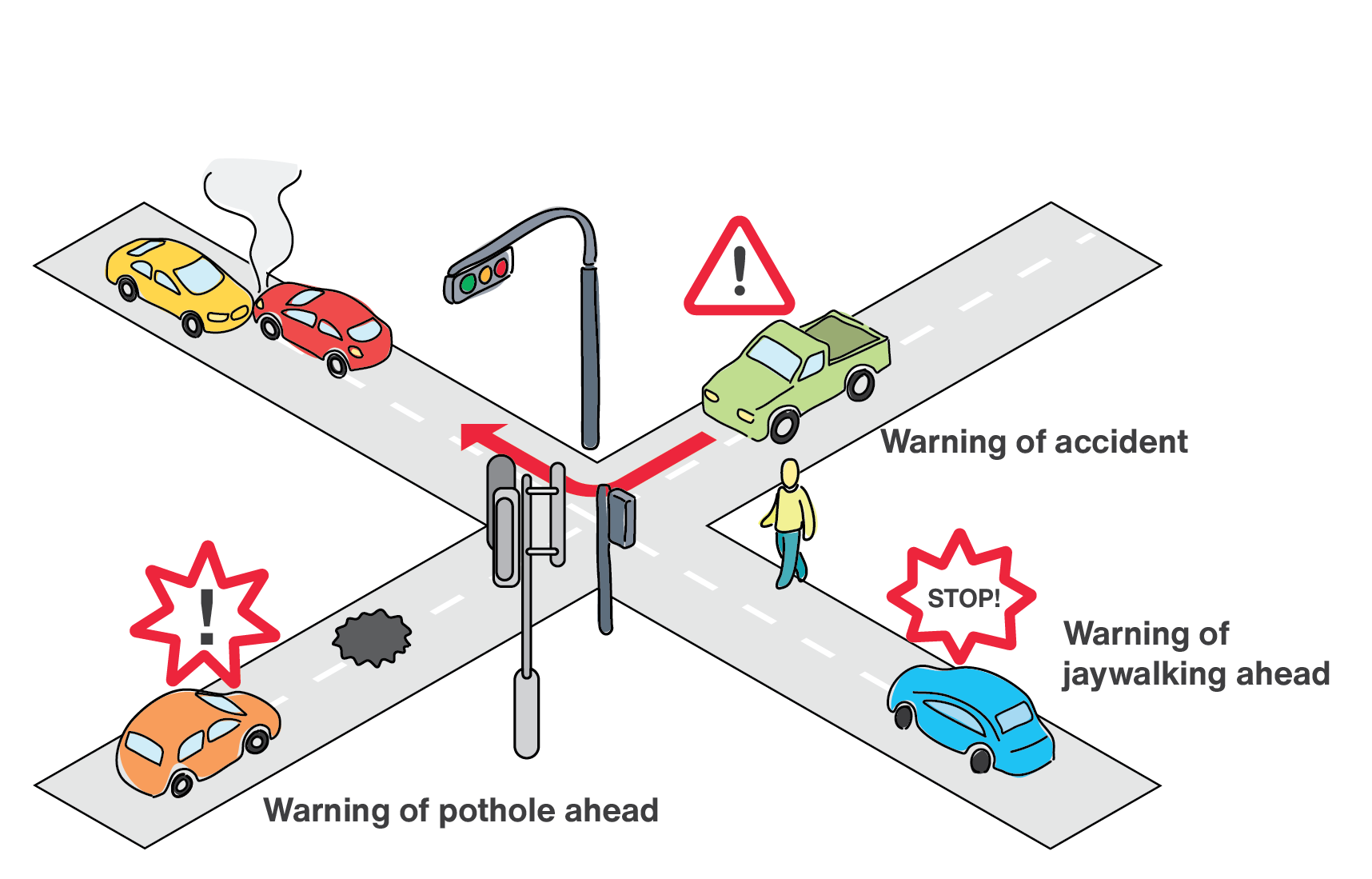
Street lighting systems can be used to share real-time data regarding traffic and road conditions among cars and other road users such as pedestrians, or cyclists. By analyzing traffic data collected from the street lighting infrastructure and the vehicles on the road, these structures are able to alarm drivers about dangerous road conditions, traffic jams, and impending safety issues ahead.
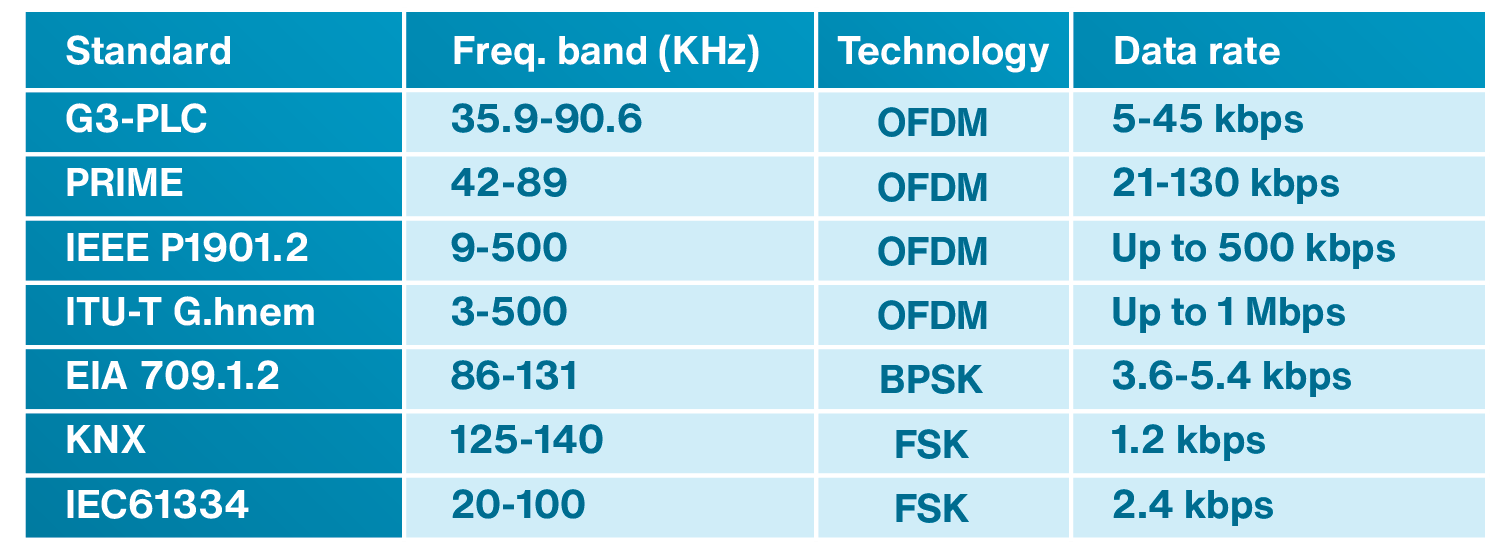
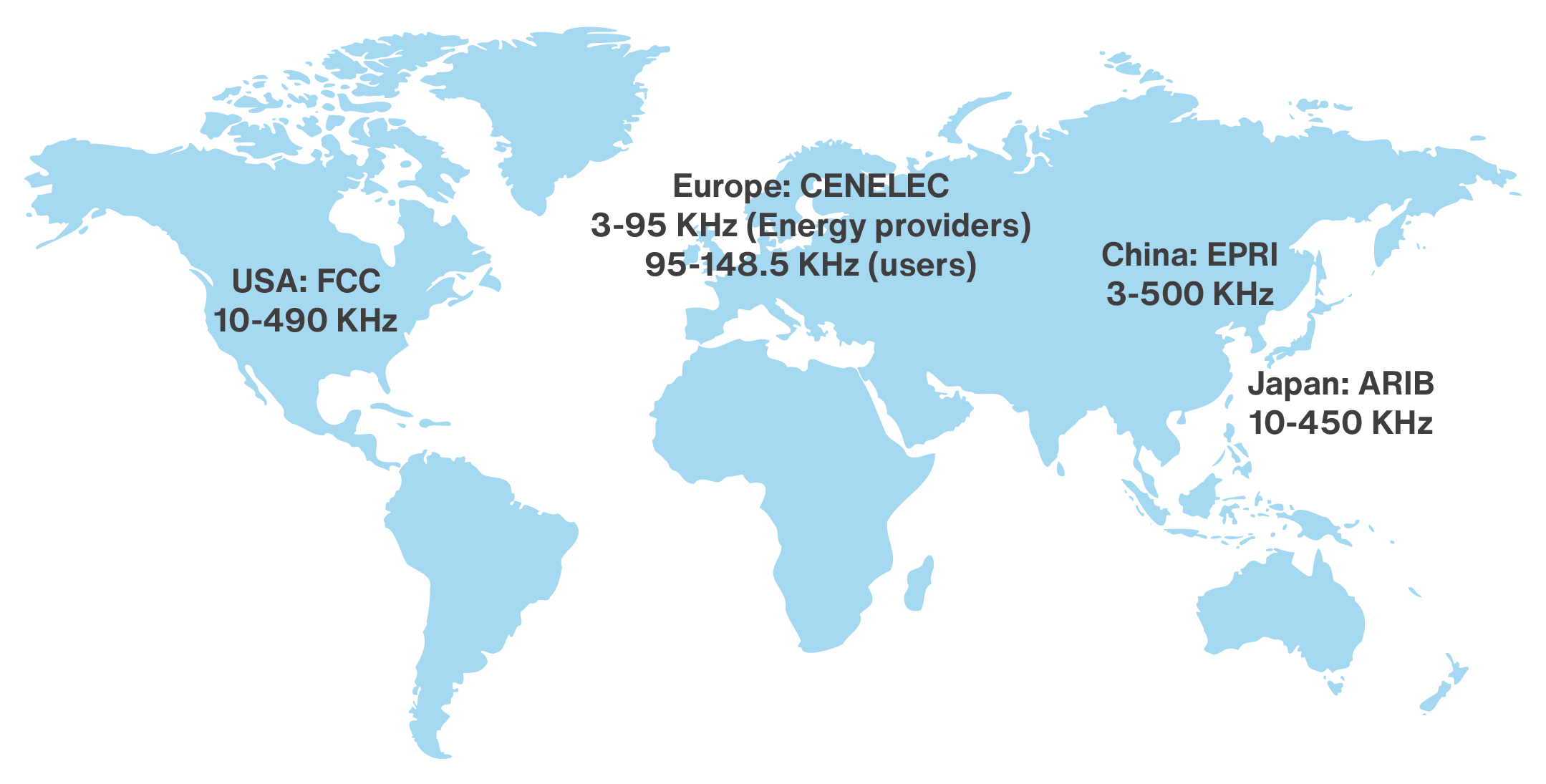
In the past, connectivity was provided to street lighting system using gateways. These gateway systems usually get connected to small parts of street lights using technologies such as Power Line Communication (PLC). The deployment of CIoT, eliminates the need for proprietary gateways. Each light pole can directly communicate with a central management platform. Easy installation is an essential need for this application, due to the existence of many street light poles in the city. CIoT provides easy installation and eliminates the need of connection to a gateway which consequently reduces the cabling and installation costs. Due to its great coverage within cities and its high reliability, CIoT can provide connectivity for applications that require low data rate connectivity such as simple light dimming as well as the ones that require high data rate such as video surveillance.
Figure 1.3 shows the connected street lighting poles as a foundation for smart city. The street poles can signal the drivers of the pedestrian jaywalking, accident that has happened further down the road, or the existence of a pothole on the road.
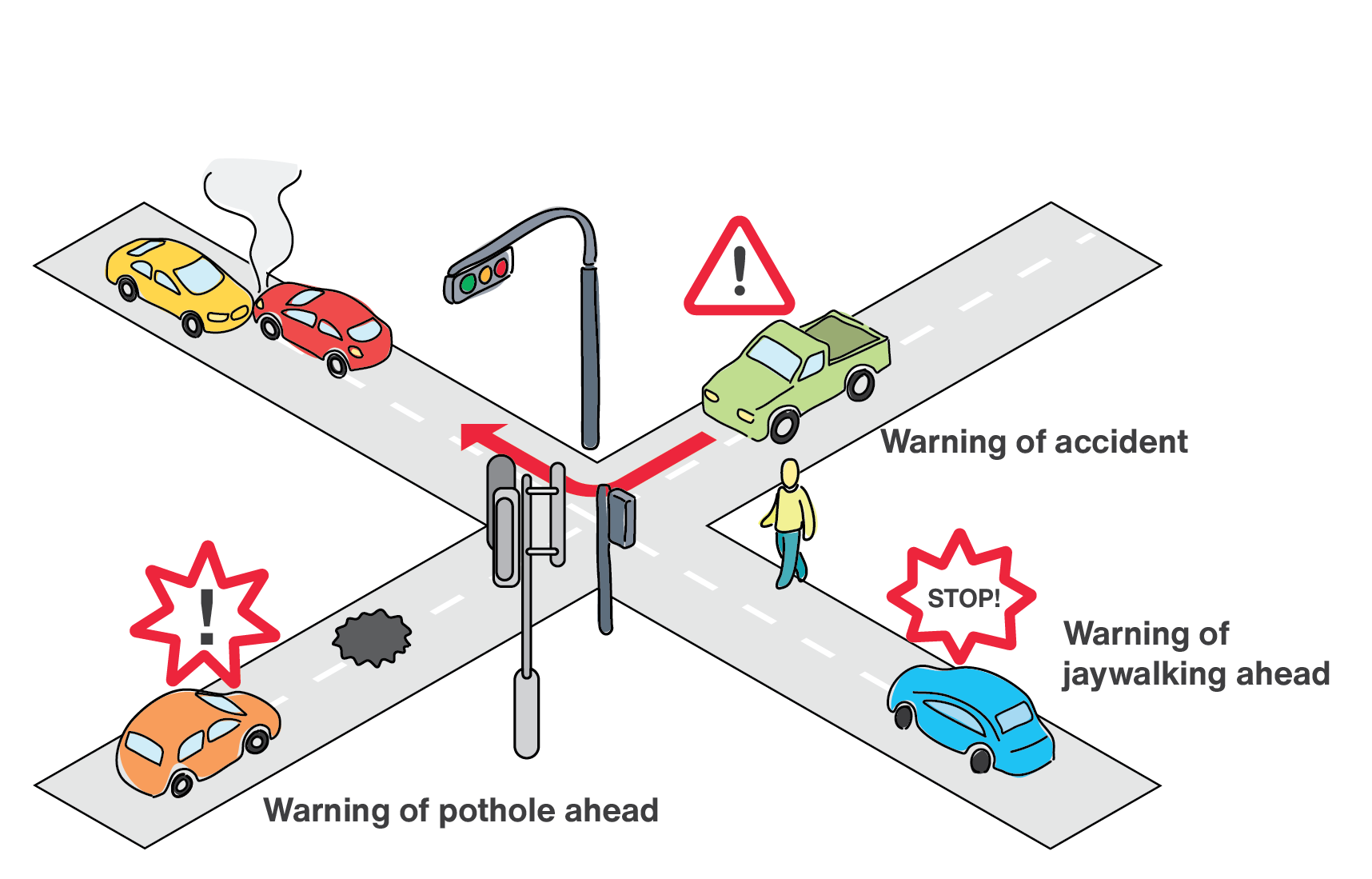
Figure 1.3: Connected street lighting pole as an IoT gateway to help drivers
In the near future, cars can communicate with road infrastructure, other vehicles and even pedestrians using IoT technologies such as cellular V2X (Vehicle-to-everything). Cellular V2X can improve road safety by generating warnings for potential hazards to the autonomous cars or smart car drivers. These warnings are delivered over the IoT network. Due to time-critical nature of these warnings, low-latency is an important factor in determining a suitable connectivity scheme. IoT with a cloud platform linking vehicles to road managed systems, bypasses the need for extensive fixed infrastructure. The handling of an entire ecosystem of interconnected vehicles and their connectivity with the road network is an important potential that can be provided by IoT technologies.
1.3.3 Industrial Use Cases
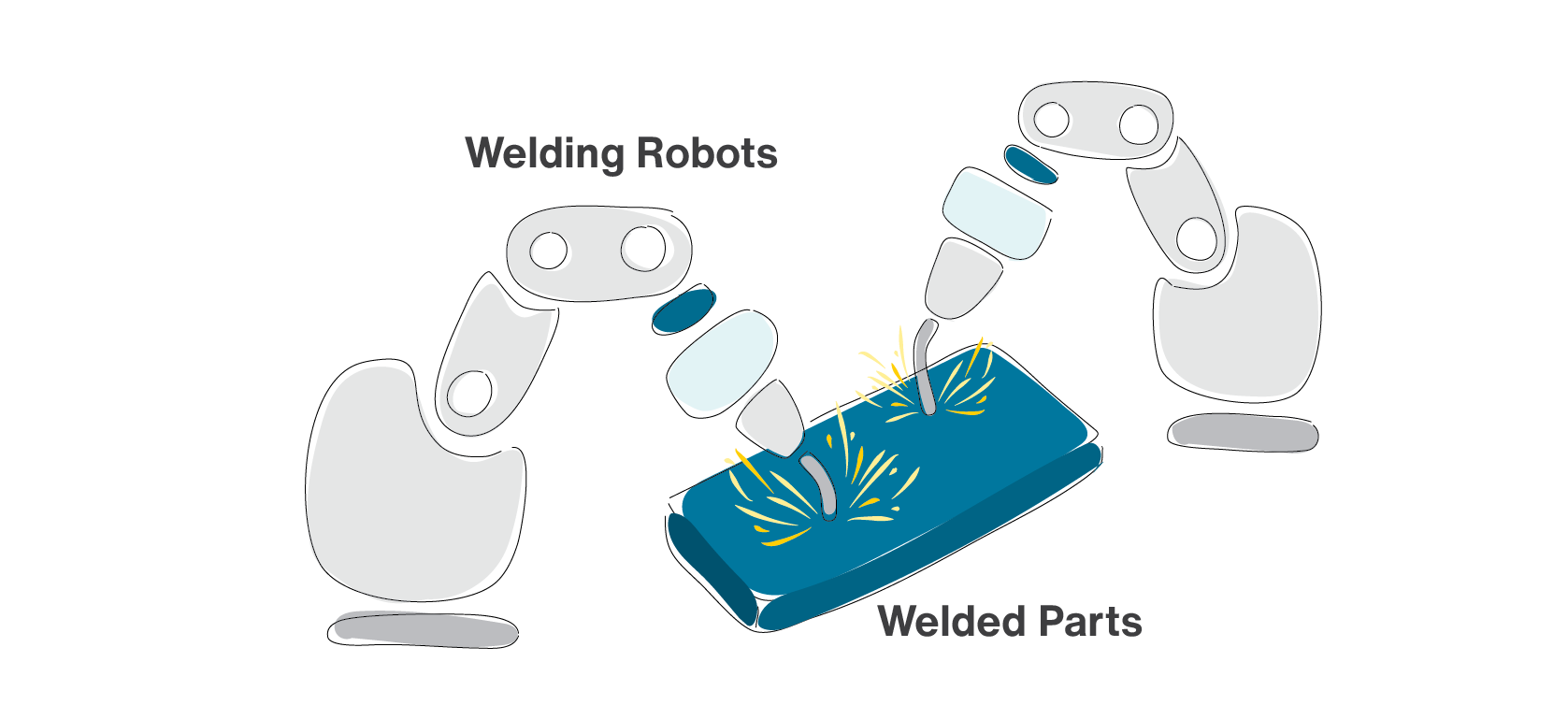
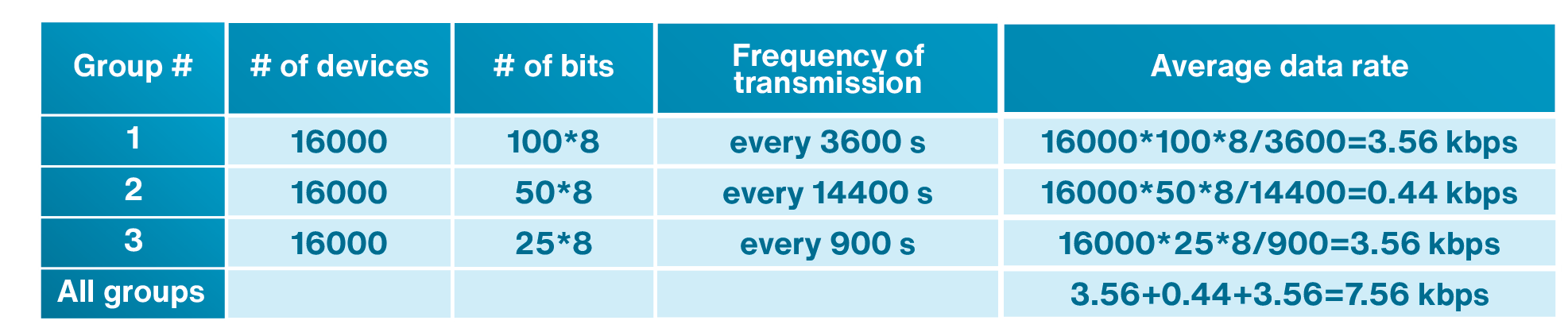
The use of IoT technologies in manufacturing is also called the Industrial Internet of Things (IIoT). Let us consider the use of IoT technology in a smart factory scenario as shown in Figure 1.4. An industrial company manufactures large machinery equipment in several different factories around the world. In each factory, 200 machinery equipment is built every day. This industrial company uses welding machine in its operation to build these equipment. Let’s assume that 500 spots need to be welded to build any of these equipment. The company collects several different information for each welding spot that can produce 15 KB of data per second. The welding process for each spot takes 10 seconds. Example of data collected from each welding spot might be the time-based voltages, currents, and temperatures of the welding machines. The data is sent to the cloud and is stored in a database. This data can be used to track possible issues in any machinery equipment.
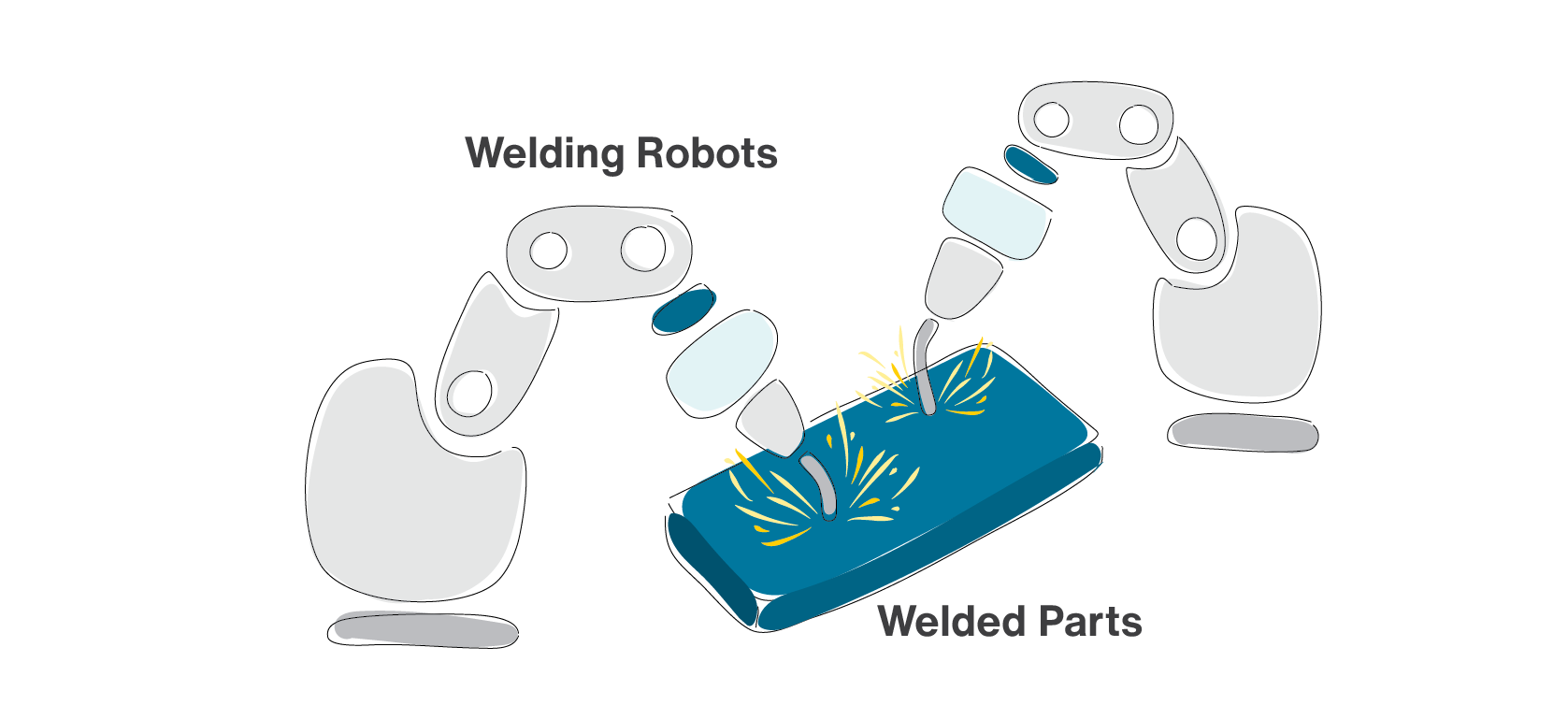
Figure 1.4: Welding robots in a smart factory generate huge amount of data
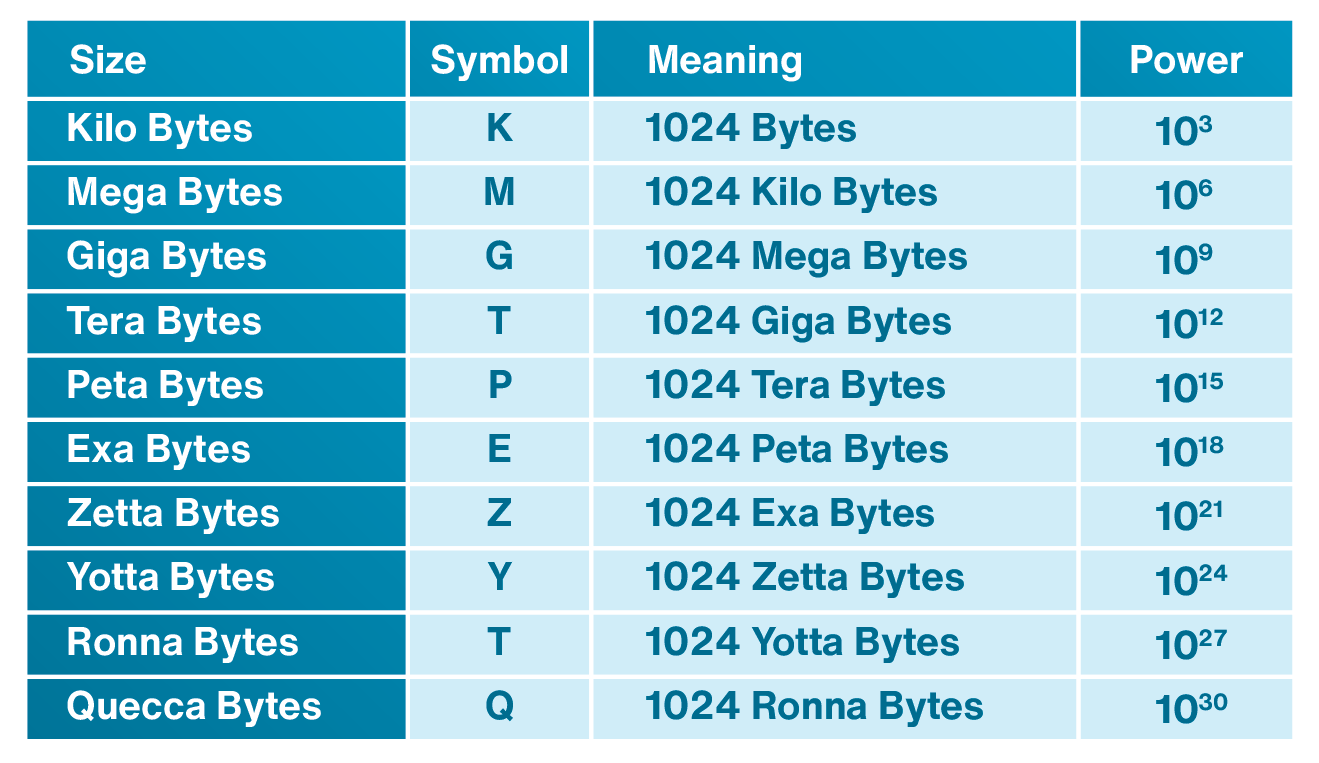
In this scenario, the company generates 15 GB of data per day from its welding machines in each factory. The welding data is not the only data that will be generated in a smart factory. The data from other operations also need to be collected. Integration and analyzing all information can be used to perform predictive maintenance, analyze the factory utilization in addition to track issues in a specific machinery equipment. A smart factory with many branches around the world can collect huge amount of data. Table 1.1 shows the symbols and units representing the size of data.
Huge amounts of data can be stored in data lakes. A data lake is a centralized storage that can store both the structured and unstructured data at any scale. Structured data uses defined data types in such a way that they are searchable and usually are stored in relational databases; while unstructured data is not as easily searchable. Unstructured data has internal structure but is not structured using defined data types or schema. Audio, and video are examples of unstructured data. The manufacturer can run different types of analytics to create insight and make better decisions. There are many use cases for data lakes in manufacturing operations management.
Table 1.1: Symbols and units representing size of data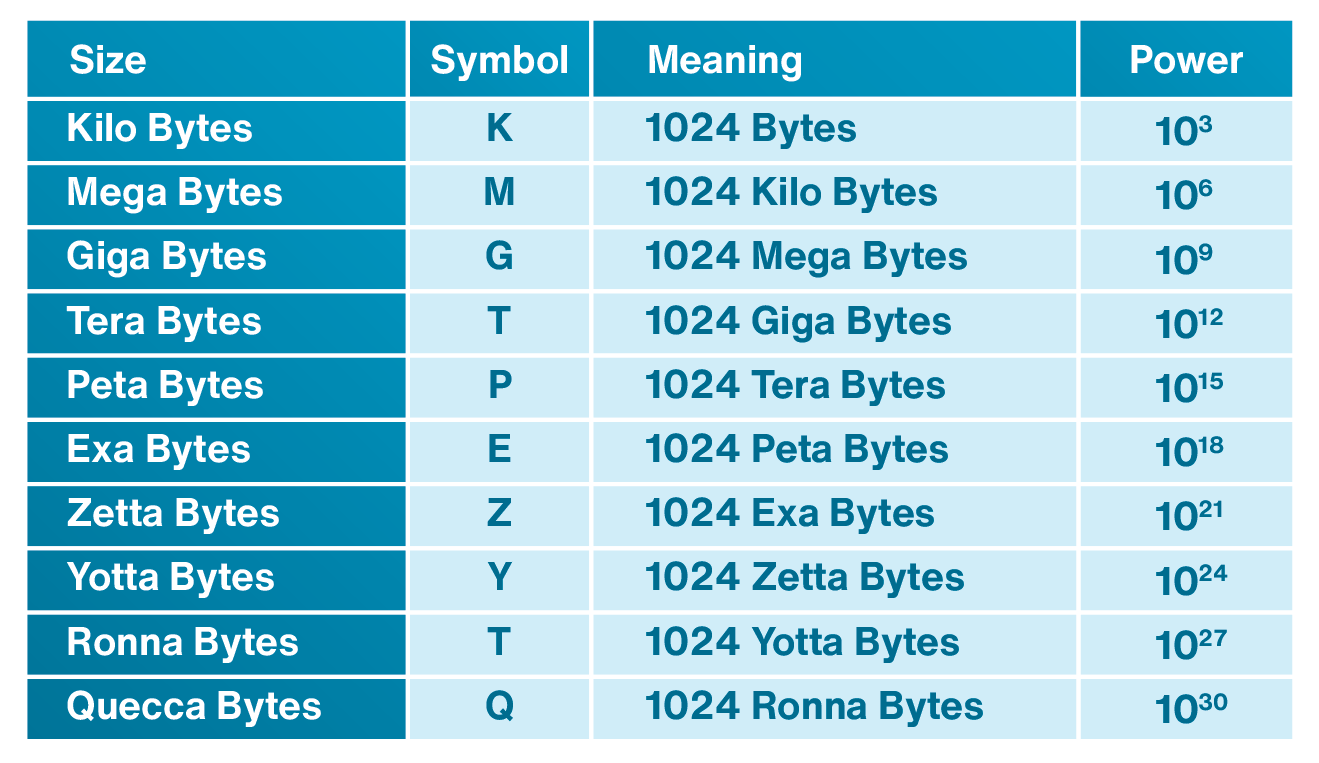
1.3.4 IoT-based Attraction Centers
IoT can bring endless opportunities to attraction centers. People visiting an attraction center can be provided with wearable wristbands to access all amenities in the center, reserve rides or buy food. These wristbands are equipped with sensors that use short-range technologies such as RFID to connect people to a network of IoT gateways connected to the Internet. Using IoT technology, the attraction center can track the actions of visitors who have worn these wearable devices and optimize their services according to the visitors’ demands. As it is shown in Figure 1.5, visitors can unlock doors and enter to different locations in the attraction center with valid admission, use fast track services to avoid the queues, and pay for the services. The wearable device acts as keys, credit cards, tickets, passes and more. The collected data is used to help the attraction center to anticipate the location, behavior, and interests of the visitors. One of the biggest challenges of any attraction center is to minimize the wait times for different attractions within the center. As each person swipes their IoT based wearable wristband at an attraction, vital information is transmitted real-time to the cloud or a private management platform through IoT gateways. This allows decisions to be made about adding staff or giving some incentives to visitors to go to another attraction in order to reduce the wait time.

Figure 1.5: Wearable wristband enables visitors to enter an attraction center.
1.3.5 Smart Grid Automation
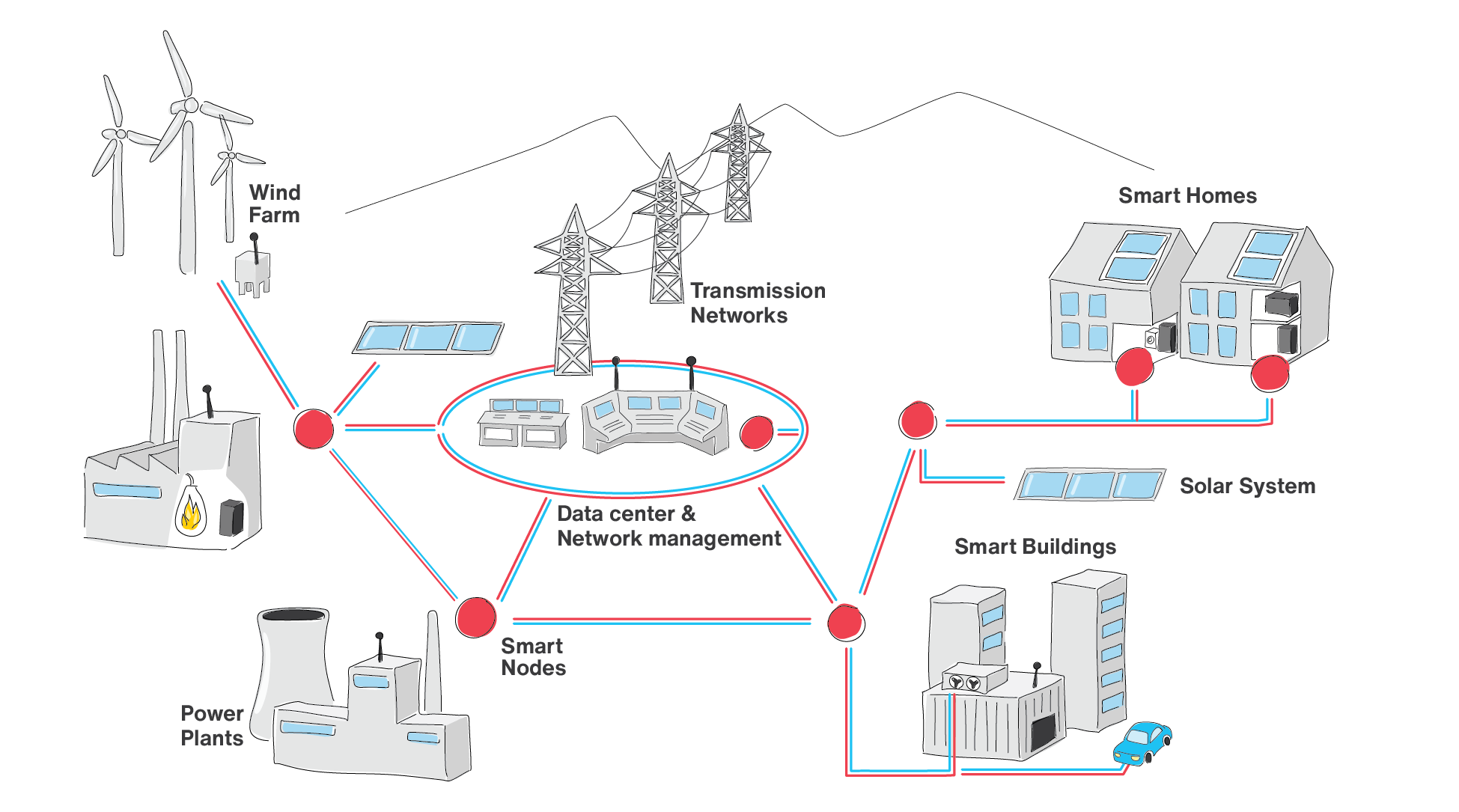
IoT technology can help in the management and automation of the smart power grid as shown in Figure 1.6. The operations and maintenance of smart grid systems need to be optimized to meet the increasingly challenging requirements of their grid caused by factors such as the integration of renewables into the power grid, and tighter regulations. Power grid also needs to detect and respond to faults along the grid rapidly. Due to large variation in energy production of renewable energy and the challenging issues of integrating the renewable power to the micro grid, a reliable smart grid network requires real-time control and management of generated energy into the grid to avoid overload. Therefore, there is an extensive signaling between all micro-grid nodes. The signaling system needs to be fast and reliable.
Wired IoT systems, and wired optical systems are mostly in use today in smart grid systems. Cellular IoT can also be used for this application. Actually, CIOT is a better choice as compared to wired alternatives due to its lower cost and higher deployment flexibility. However, the wireless technology needs to provide a similar level of performance in terms of latency, data rate, and security.
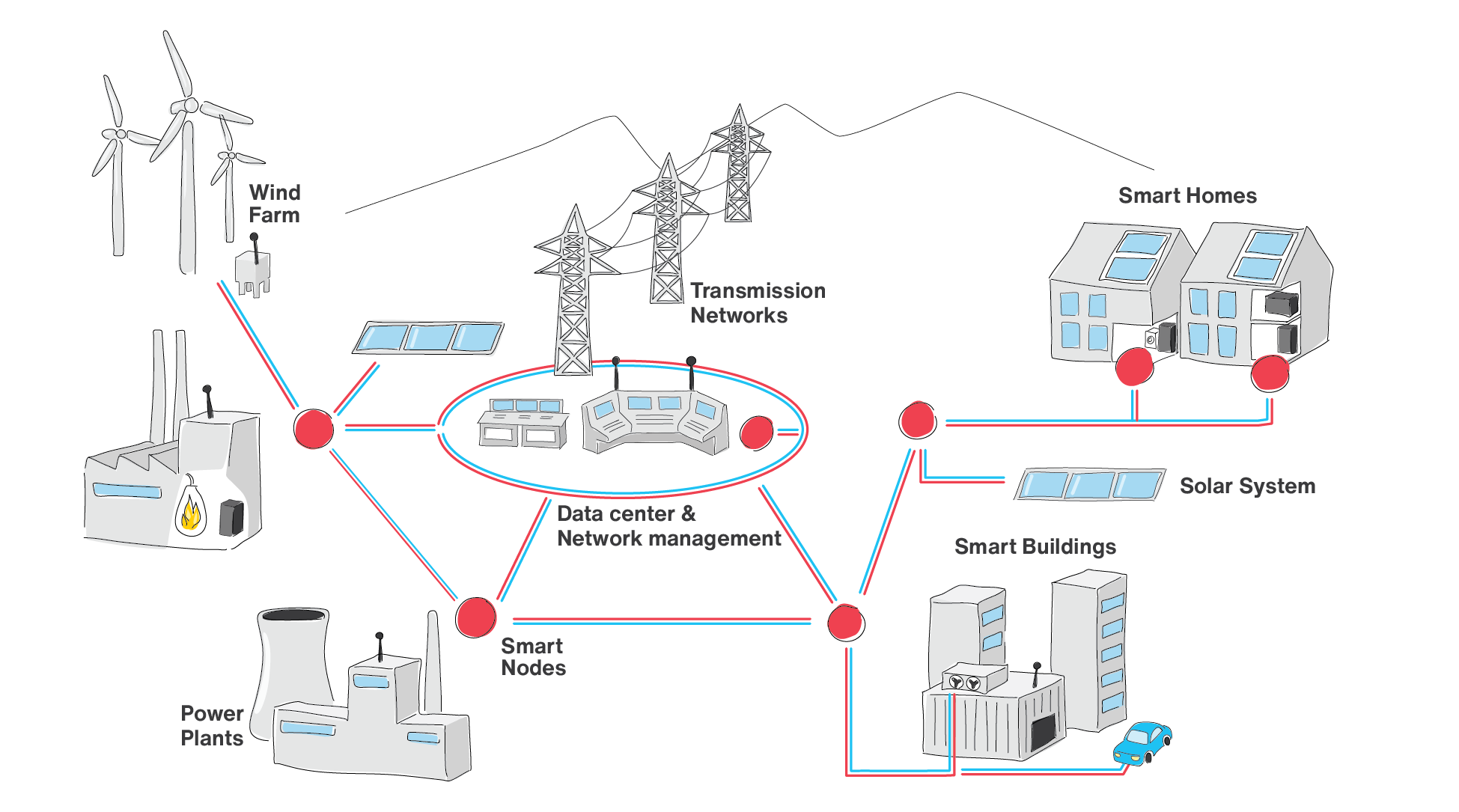
Figure 1.6: IoT technology helps in the management and automation of the smart power grid
1.3.6 Collaborative Robots
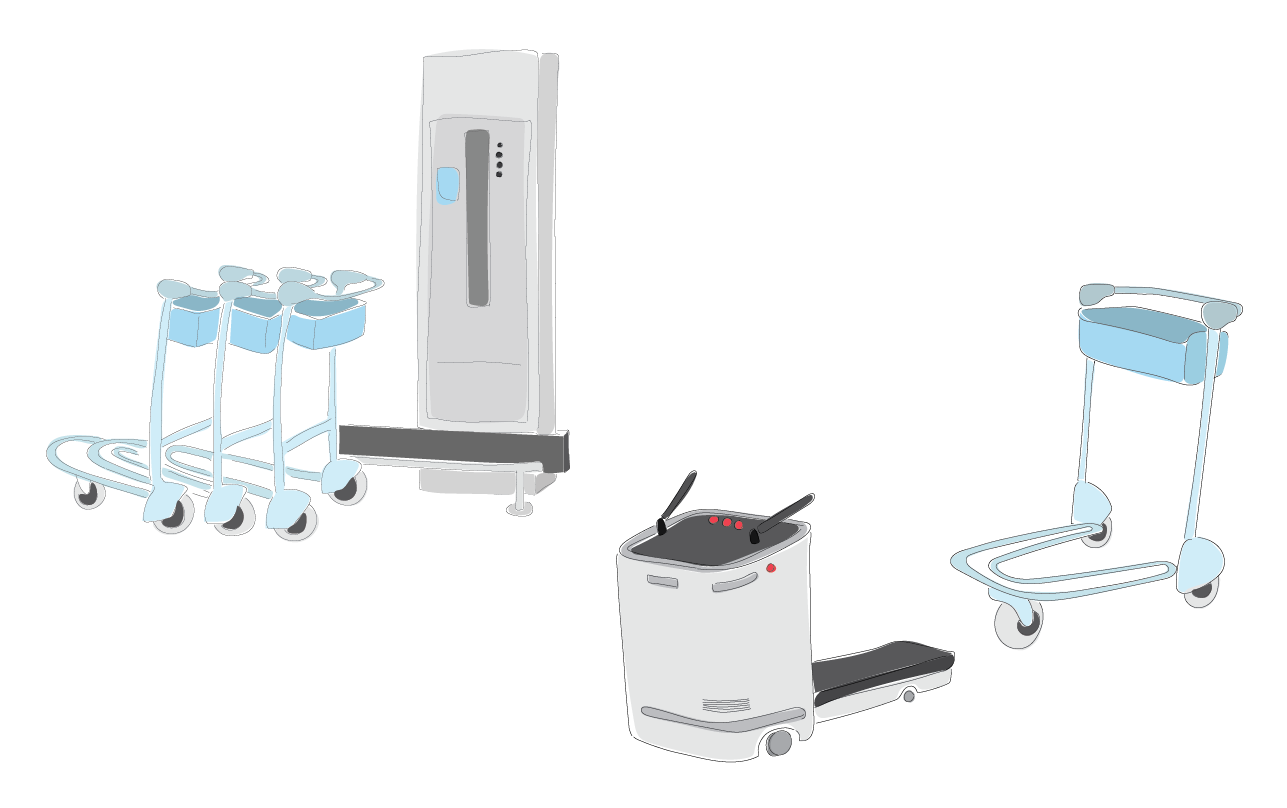
IoT technology can be used in orchestrating the operation of arm and mobile robots as shown in Figure 1.7. To be able to autonomously perform various tasks, each of these robots need to have many sensors as well as powerful processors to operate individually. There is a need for a centralized management system and more processing power to enable several robots to complete a complex task. It should be noted that providing enough processing power into these robots can be very costly, in particular for smaller robots. Providing connectivity using wired IoT might be challenging in situations where the robot is mobile such as Automated Guided Vehicles (AGV). Wireless IoT technology can be a better choice, but it should be able to provide the low latency requirement needed for this application. Using IoT technology, the robotic system can then offload part or all of this processing to the edge or cloud. Cloud computing of the data collected from each robot can be used to orchestrate the operations of each robot in a collaborative robots scenario.
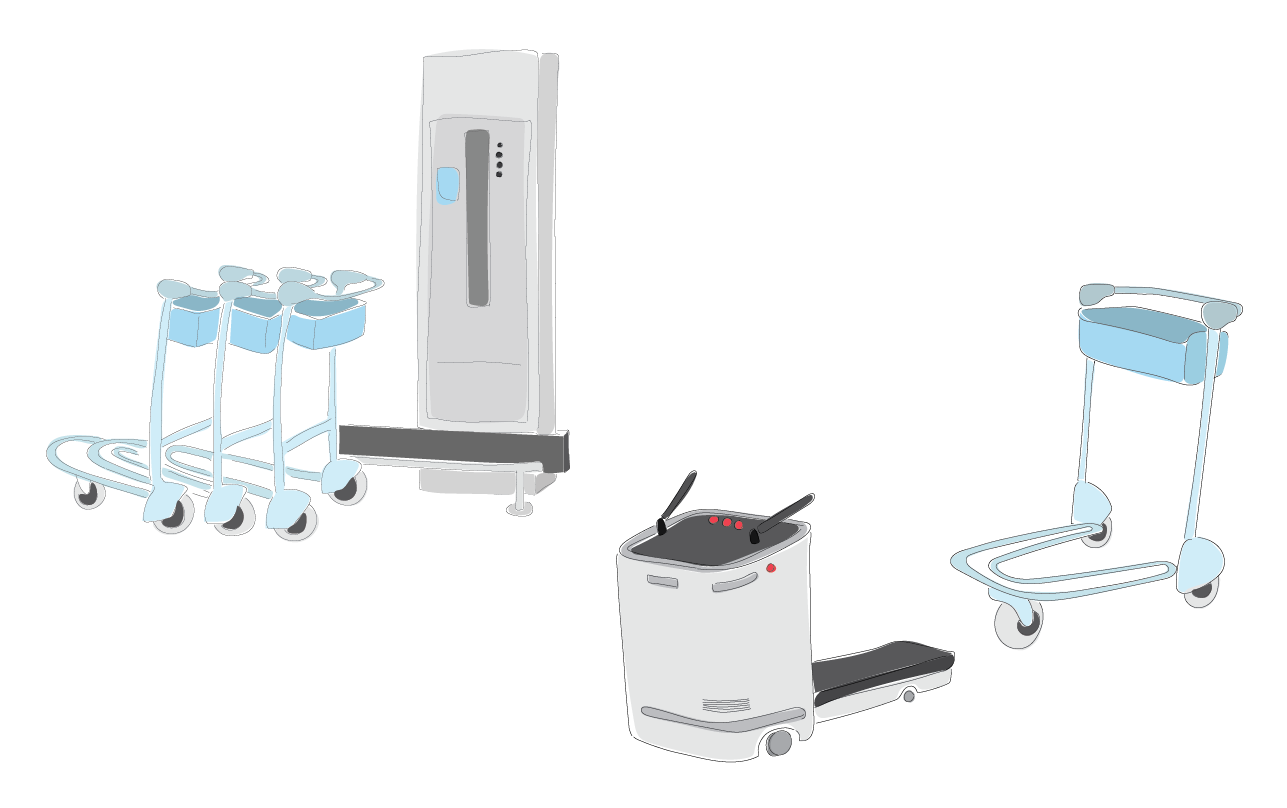
Figure 1.7: IoT technology used in orchestrating the operation of mobile robots
1.3.7 Video Surveillance
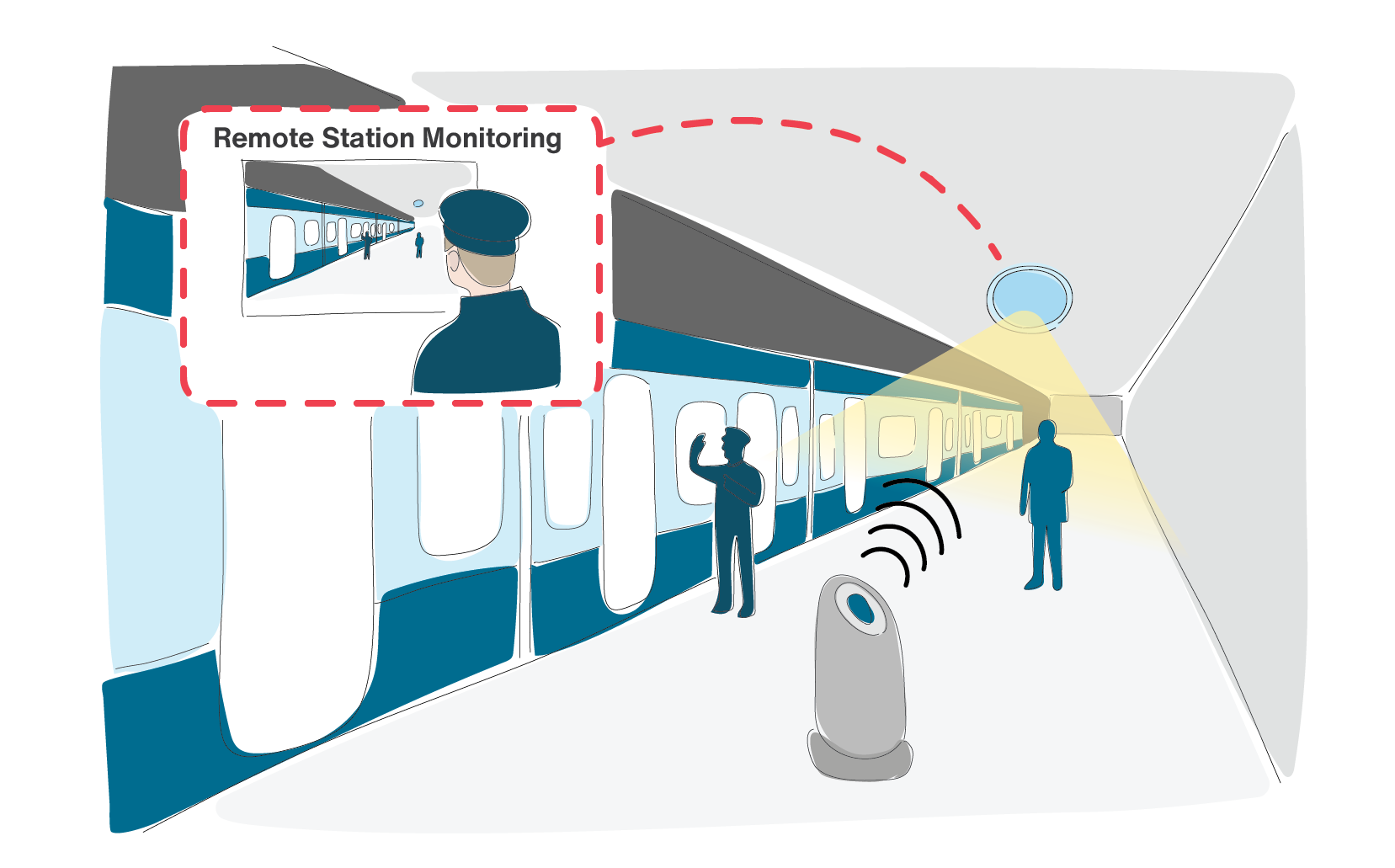
To provide public safety in airports, transportation stations, or public events such as concerts, festivals, and election rallies, IoT-based public surveillance and security systems can be used. In general, IoT-based surveillance systems connect one or several cameras to the Internet directly or through IoT-gateways. Beside static installations, the surveillance system might be mobile. This includes cameras installed on vehicles such as police cars, buses and trains used in public transportation, wearable cameras worn by law enforcement officers, or even surveillance drones. Figure 1.8 shows an IoT-based surveillance system for a train station.
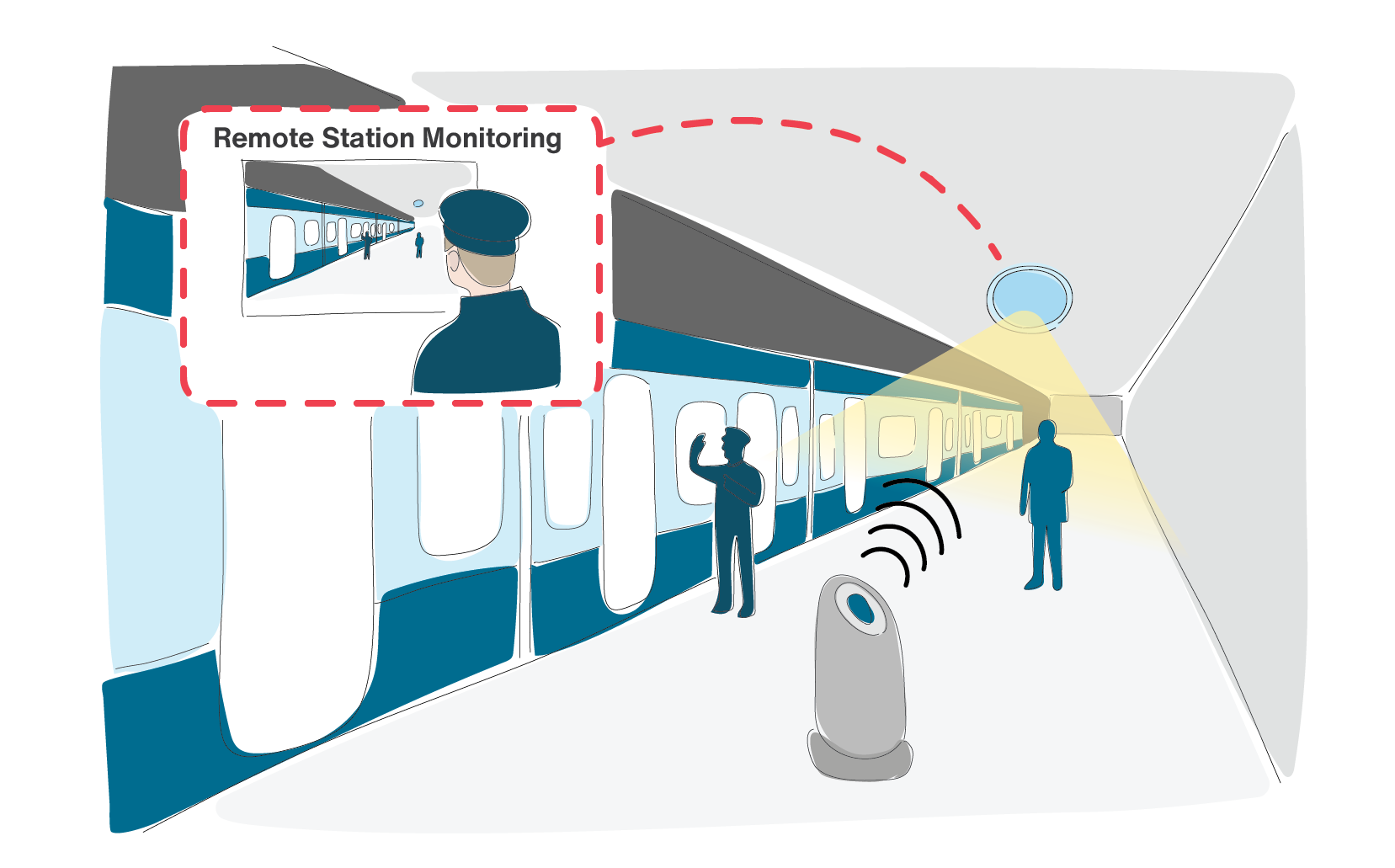
Figure 1.8: IoT-based metro station showing several cameras as part of its surveillance system. A fixed camera installed on the celling, and a mobile cart carrying a camera. The station is monitored remotely.
1.3.8 IoT-based Hand Sanitizing Station
The patients in hospitals and clinics may carry and spread different types of germs, bacteria and infectious diseases. This problem does not only belong to medical facilities. In any organization, people use their hands to open doors, shake hands with other people which expose their hands to germs and bacteria. Since a single doorknob could be touched by many people, it can cause spreading the disease in a workplace. Meeting rooms are often packed with employees, as well as clients who exchange handshakes, thus swapping germs. Installing hand sanitizer stations in an organization and encouraging regular use of these stations can lead to having a healthier work environment. In case of an epidemic or pandemic, installing hand sanitizer stations would be very effective. IoT-based hand sanitizing stations are sensor-activated and provide staff in an organization with sanitation reminders. These hand sanitizing stations are all connected directly to the Internet or via an IoT gateway. The sensors can identify each employee and record hand hygiene events. The system records when an employee enters or exits a room, and gives the employee specific amount of time to use any of the sanitizing stations in the area.
1.3.9 Railway Switch Monitoring System
Switches are one of the most important parts of a railway network. An unfortunate issue can arise when a mechanical part of a switch wears out, or fails to operate. These issues do not usually reveal themselves by regular inspections. An IoT-based switch monitoring system can collect several data from the switch such as the timing of switch operations, motor voltage and currents, and vibrations. Vibrations can be measured when the train passes, and with big data analytics, trends can be analyzed. Evaluation of this data will show deterioration of the switch mechanisms as well as the dynamic behavior of the switch under different weather conditions. Real-time warnings can be issued to the operation center when measurements indicate imminent failure.
1.3.10 Elevators at Railway Stations
The availability of elevators in the public transportation stations is important especially for the disabled or elderly customers and those with child carriages. IoT technology can help increase the availability as well as improved accessibility and safety for commuters. Integration of elevators from multiple manufacturers into one integrated monitoring platform, visibility into the real-time elevators status for passengers and commuters, predictive maintenance and improvement of elevators reliability and safety based on failure data, are examples of benefits that an IoT system can provide for this application. An IoT device installed in an elevator can monitor the changes in operating data. Examples of collected data are temperature, friction, tilt, or noise. Based on the real time data and analytics, it is possible to predict when the elevator needs maintenance. Not having insight on the elevator’s conditions could result in equipment failure, and in turn causes disruptions. IoT devices can be used to keep track of wear and tear and use the information to predict the time that the maintenance will become necessary. The door open-close cycles, the amount of time it takes for the door to be closed, the amount of current it draws to open or close the door, the number of times the elevator’s door has been opened from the last service can be examples of data used for predictive maintenance.
1.3.11 Smart Parking
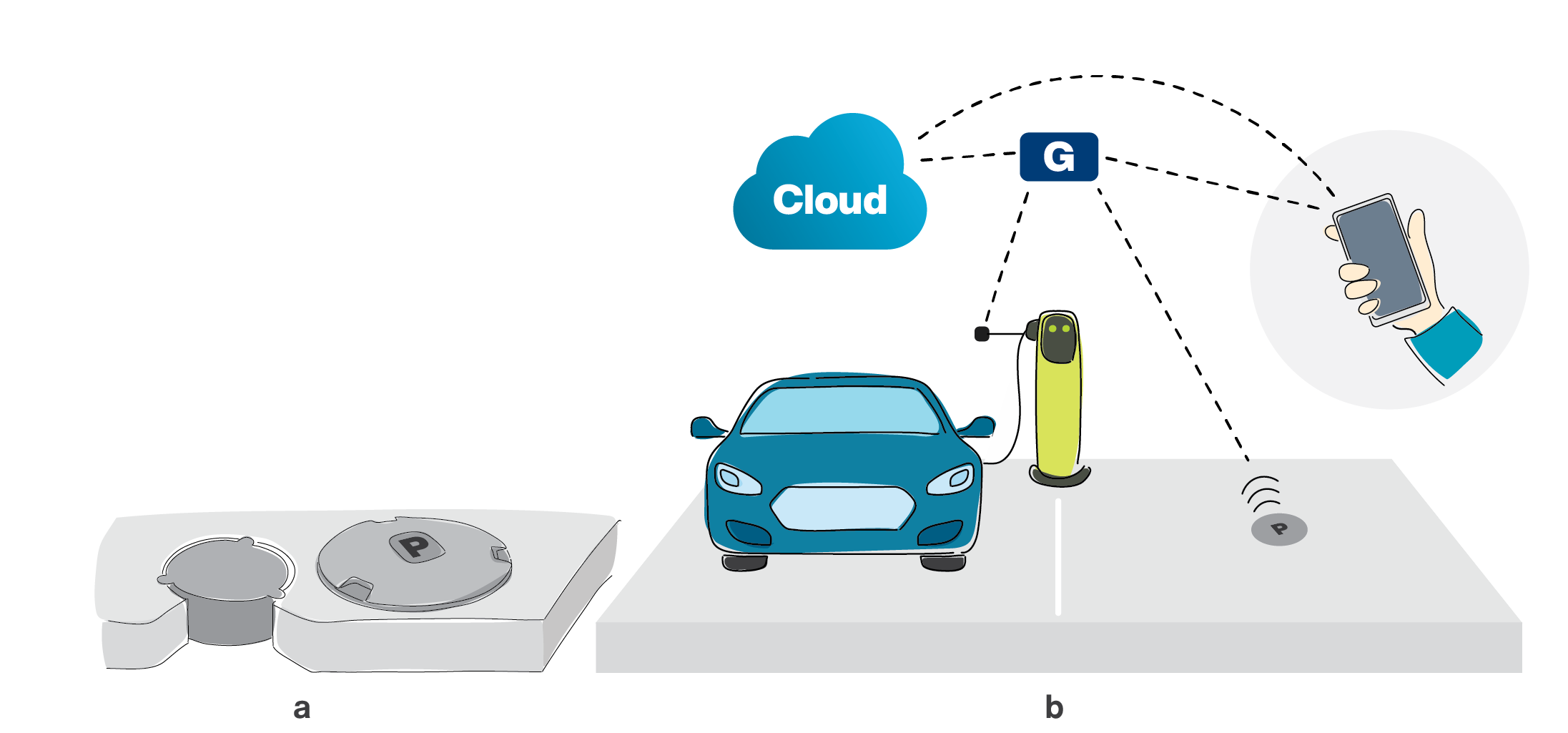
Smart parking systems can detect the number of available parking spots as well as the locations of the cars parked in the parking lot. Smart parking system can also inform or guide the customers to vacant parking spots. In a busy parking lot, people may spend a lot of time trying to find a vacant parking location while they might none be available. IoT technology can provide the customers of a smart parking with real-time information in regards to the locations of available parking spaces.
In-ground or surface-mounted smart parking sensors that communicate with an IoT gateway can provide real-time parking data over the Internet. Figure 1.9.a shows an example of in-ground or surface-mounted smart parking sensor. Figure 1.9.b shows an application of smart parking using these sensors. The sensor provides an accurate vehicle detection in parking spaces using an IoT connectivity method. The collected information from the sensors can be saved on a local server or on the cloud. This information can be utilized by other applications and third parties such as parking management systems, parking enforcement, and mobile payment system that can utilize that data to provide further services to their customers.
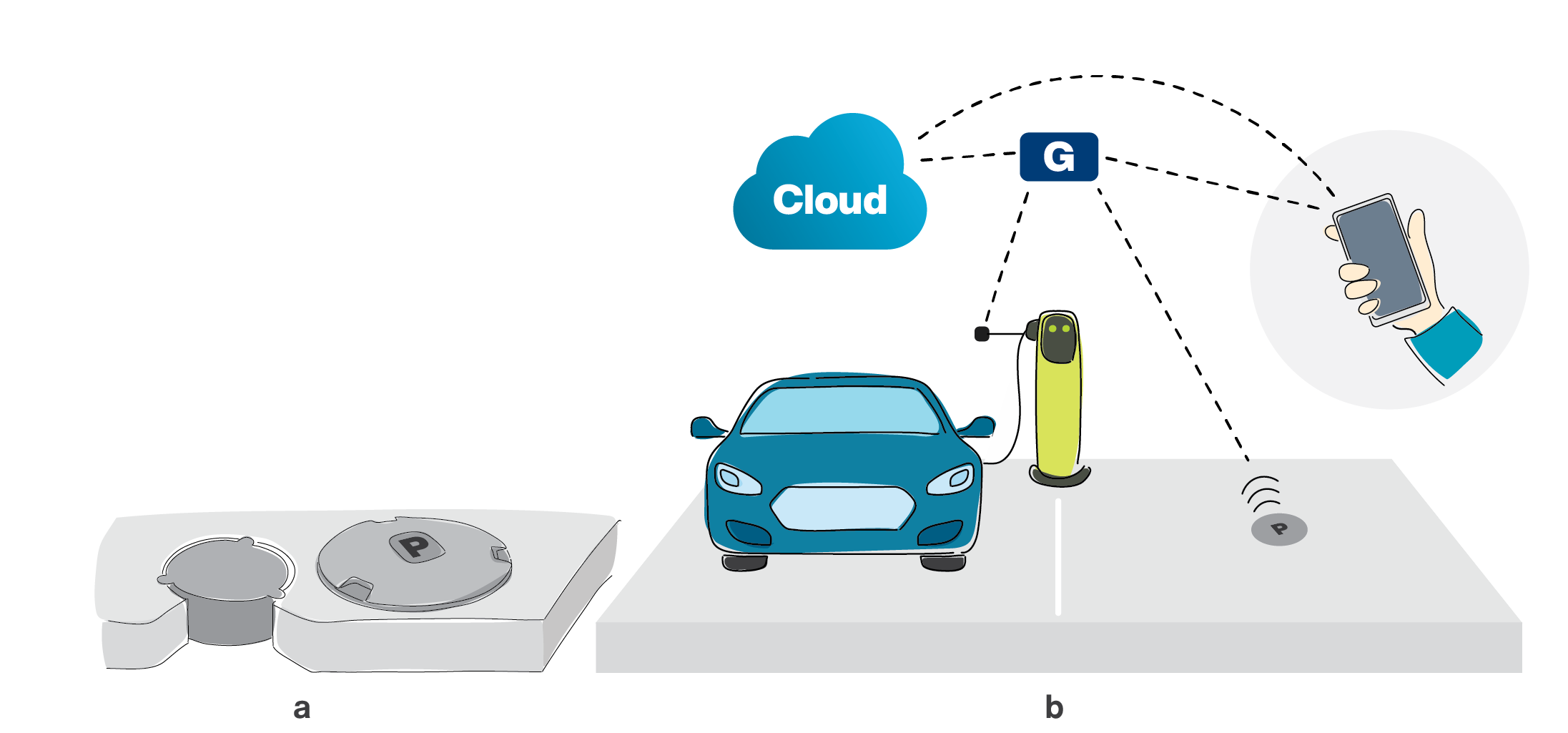
Figure 1.9: a) In-ground and surface-mounted smart parking sensors b) Smart parking system
1.3.12 IoT for Worker Safety
Construction industry suffers from high worker fatalities at construction and work sites every year caused by issues such as falls, electrocutions, risks associated with interacting with dangerous machinery, or being caught in or between objects. Despite advances in science and technology, works in challenging work environments will continue to exist. We can see similar problems in many other industries such as oil and gas, and mining where workers are remote and work in hazardous environments that present many challenges in regards to safety. For example, it is extremely challenging to extend oversight when workers are around heavy equipment, on a remote off-shore drilling rig, working on an underground location, performing inspection on telecommunication cell towers, or working in chemical processing plants.
Wearable IoT can provide worker safety, and reduce or eliminate many risks by collecting and analyzing real-time safety data to identify and prevent hazardous conditions before they happen. For example, for the operators of dangerous machinery equipment, a fatigue detection wearable IoT device can increase the safety of the workers on a construction site. A wearable device can also detect hazardous conditions in advance or collect the air quality data and alert the workers on the site. In the above mentioned scenarios, wearable IoT can ensure the workers’ health or reduce risks for workers as well as costs for the employers. In general, IoT technology is used to monitor workers, sites, and equipment by collecting and analyzing sensor data in order to change the processes, or trigger alarms that can minimize the risks and the impact of possible incidents. The result of integration of IoT technology with analytics brings visibility to the situation of workers in extremely challenging environments.
- Two similar applications, belonging to different use cases of the same vertical
- might be quite different in terms of their platforms, and processing, but are similar in terms of their regulatory bodies, and standards.
- might be quite different in terms of their platforms, processing, regulatory bodies, and standards.
- might be quite different in terms of their regulatory bodies, and standards, but are similar in terms of their platforms, and processing.
- are most likely similar in terms of their platforms, processing, regulatory bodies, and standards.
- In what sense the IoT traffic is not the same as the traffic generated by human?
- IoT traffic is mostly periodic during the day, but human traffic is not.
- IoT uplink traffic is usually more than downlink, while it is the other way around for human generated traffic.
- IoT devices can generate very small or very large amount of data, while the traffic generated by human is typically large.
- All of the above
- A wireless sensor network is _____
- an IoT network, if the number of devices are more than a threshold
- an IoT network, if it is connected to the Internet
- an IoT network, if it consumes low energy
- not an IoT network
- The term “Internet of Things” was first used by
- Kevin Ashton, to promote Radio Frequency Identification (RFID) technology
- Elon Musk, to introduce connected cars
- Charlie Kindel to introduce Alexa Smart Home
- Greg Kahn, to establish Internet of Things Consortium
- Why is there a need for IoT gateway?
- To enable many IoT devices with different connectivity methods or protocols to connect to the Internet via the gateway
- To provide security in connection to the Internet
- To provide computation for IoT devices
- To provide data storage for IoT devices
- Can IoT devices also play the role of IoT gateway?
- Yes, but only one IoT device can become the IoT gateway
- Yes, several IoT devices in the network may play the role of the IoT gateway
- No, IoT devices can not become IoT gateways
- No, unless many IoT devices lose their connection to the Internet
- For stationary IoT devices directly connected to the power source and not using batteries, is low power consumption still a requirement?
- No, low power consumption is typically a requirement for battery operated devices.
- No, low power consumption is typically a requirement for mobile IoT devices that use wireless connectivity.
- Yes, due to existence of massive number of IoT devices, reducing the power consumption of each device reduces the energy that is needed to be produced to power these devices.
- It depends on the standard and protocol used for the IoT devices.
- What is the principal idea to reduce the power consumption of IoT devices?
- Reduce the transmit power level.
- Increase the reception sensitivity level.
- The IoT device needs to go to sleep if it does not have anything to perform.
- The IoT device aggregates its traffic to be sent as a larger chunk.
- Technologies such as WiFi, BLE or Zigbee are part of
- Licenced LPWAN
- Un-licenced LPWAN
- Both A and B
- Non of the above
- IIOT stands for
- Information Internet of Things
- Intelligent Internet of Things
- Industrial Internet of Things
- Infrastructural Internet of Things
- Can IoT devices be used for medical purposes to treat the patients automatically?
- No, IoT devices can only collect health data for monitoring purposes.
- No, the collected health data can be analyzed to find a good course of action for treatment but cannot treat the patients.
- No, by analyzing the collected data, the information for treatment can be sent to a doctor’s office, but not to the IoT device.
- Yes, by analyzing the collected data, the information for treatment can be sent to the IoT device. The IoT device should have the equipment needed for treatment.
- What are the sensor(s) and connectivity options that you can find on an IoT medical device for a person with no mobility issues?
- An IoT device can have just one sensor such as body temperature sensor. The connectivity should be wireless.
- An IoT device can have one or several sensors such as body temperature, pulse, blood pressure. The connectivity should be wireless due to the patient’s mobility.
- An IoT device can have one or several sensors such as body temperature, pulse, blood pressure. The connectivity should be wired connection for security purposes.
- An IoT device can have just one sensor such as body temperature sensor. The connectivity should be wired connection for security purposes.
- Assume that IoT applications have generated more than 500 zettabytes of data in 2019. If the number of generated data increases by 4 times in 2020, how much data is generated in this year?
- 2 Exabytes
- 2 Yottabytes
- 2 Ronnabytes
- 2 Queccabytes
- Which of the following is an example for smart grid edge device that plays the role of IoT gateway in utility use cases?
- Smart Meter
- Smart Home
- Smart phone
- Smart plug
To find the trajectory of a bird during a year, an IoT device is installed on the body of the bird. Explain what types of IoT connectivity schemes can be used for this application?
Explain how a smart helmet can provide emergency support in case of an accident. Use a smart phone as an IoT gateway for this application.
Describe how a smart racket can be beneficial to train the tennis players.
Give an example of an IoT system that provides safety for the driver of a vehicle.
In the scenario explained in section 1.3.3, it was written that the industrial company generates 15 GB of data per day from its welding machines in each factory. Show how this has been calculated.
Answers to Exercises and Review questions are located at the end of the book: Chapter 1 Answers


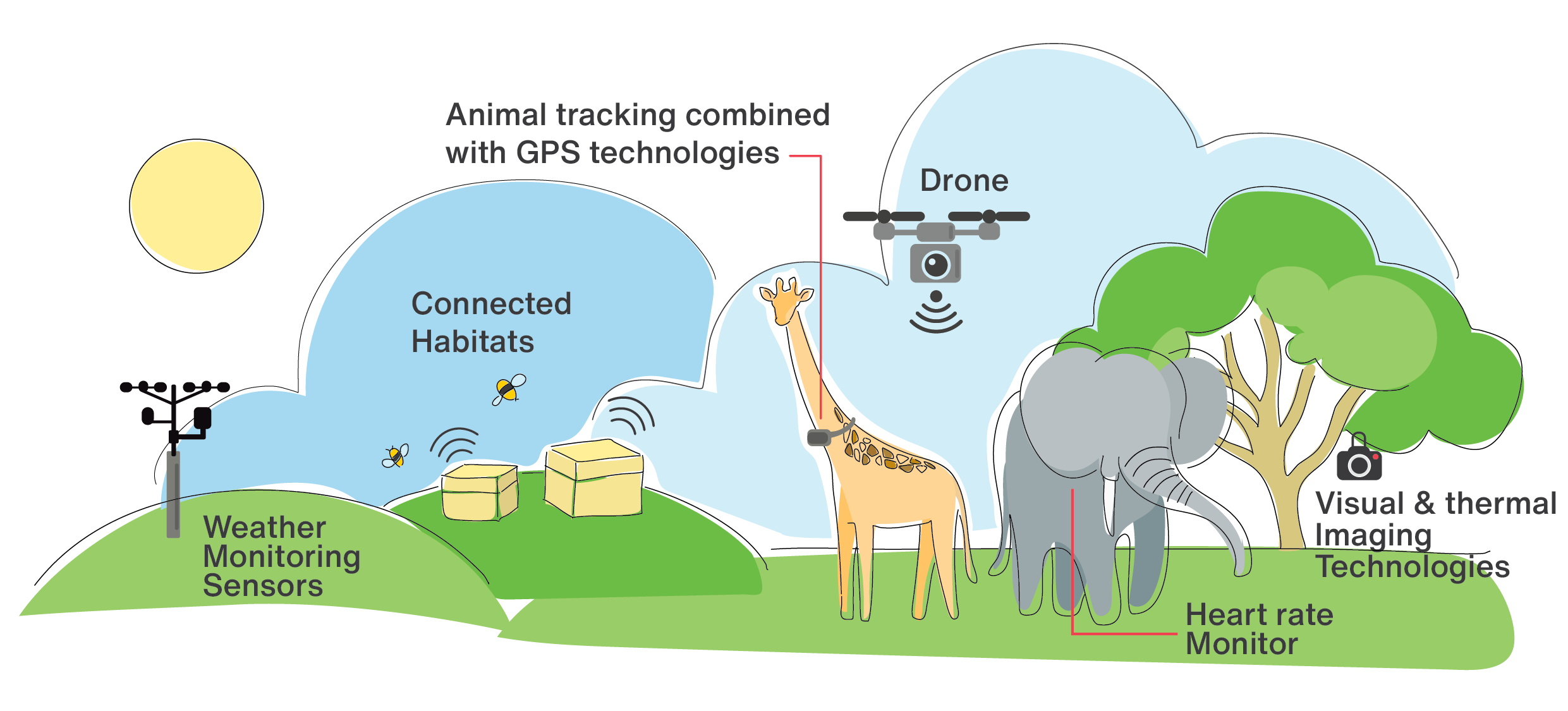 Figure 1.2: Use of IoT technology for research purposes on animal behavior
Figure 1.2: Use of IoT technology for research purposes on animal behavior