Appendix A
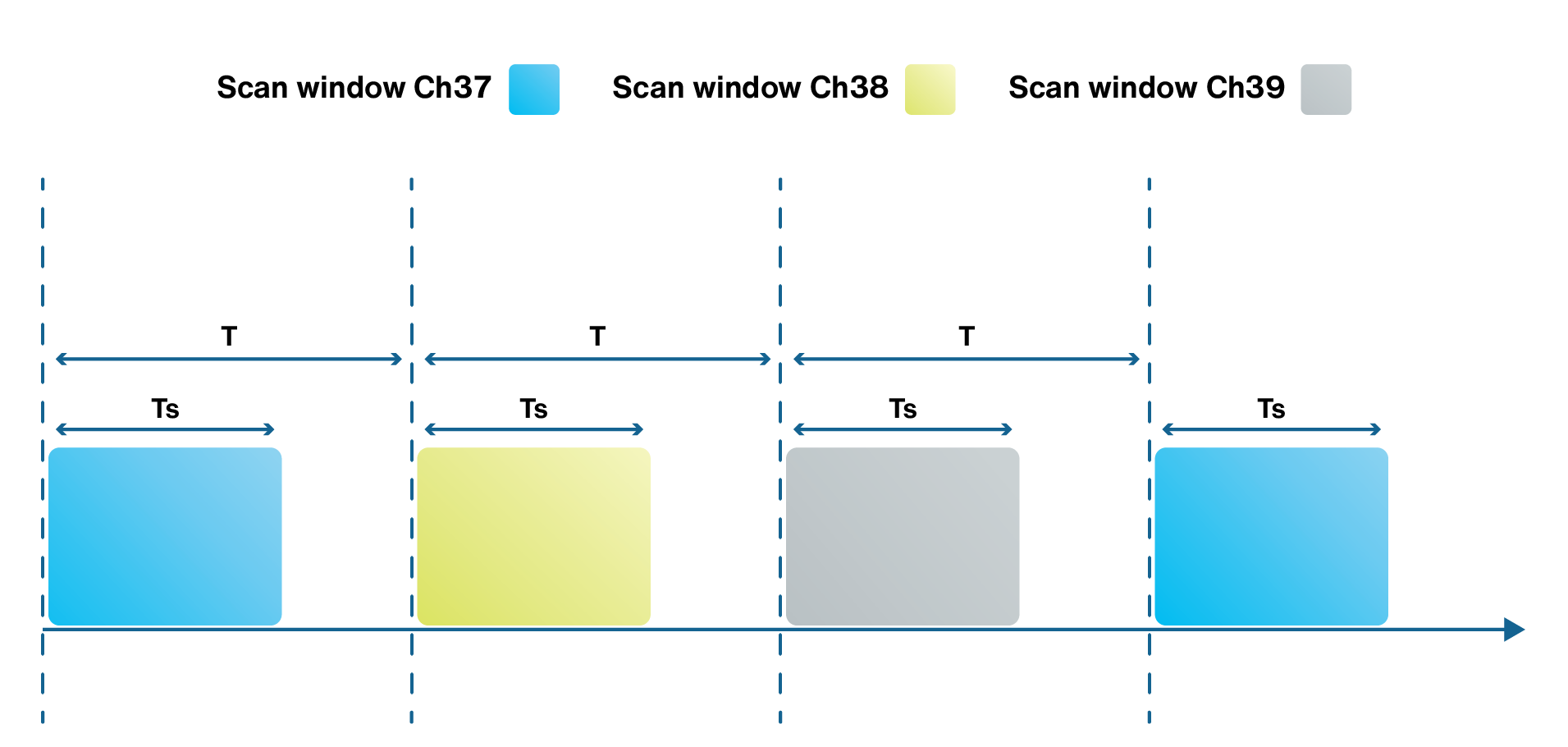
In BLE terminology, scan interval (T) is the duration of time between two consecutive times that the scanner wakes up to receive the advertising messages. The scan interval is shown in Figure A.1. When the scanner wakes up, it enables its reception to be able to listen to the advertising messages for a duration of TS, which is called the scan window. The value of scan interval should always be greater than or equal to the scan window. The values of T and TS should always be in the range of 0 ≤ TS≤ T≤ 10.24 s. In general, BLE modules use three different channels for advertising which are called Channel 37, 38 and 39. When a BLE module becomes a scanner or initiator, it scans these three advertising channels one by one in sequence of Channel 37, 38, and 39, according to a round-robin fashion, as shown in Figure A.1.
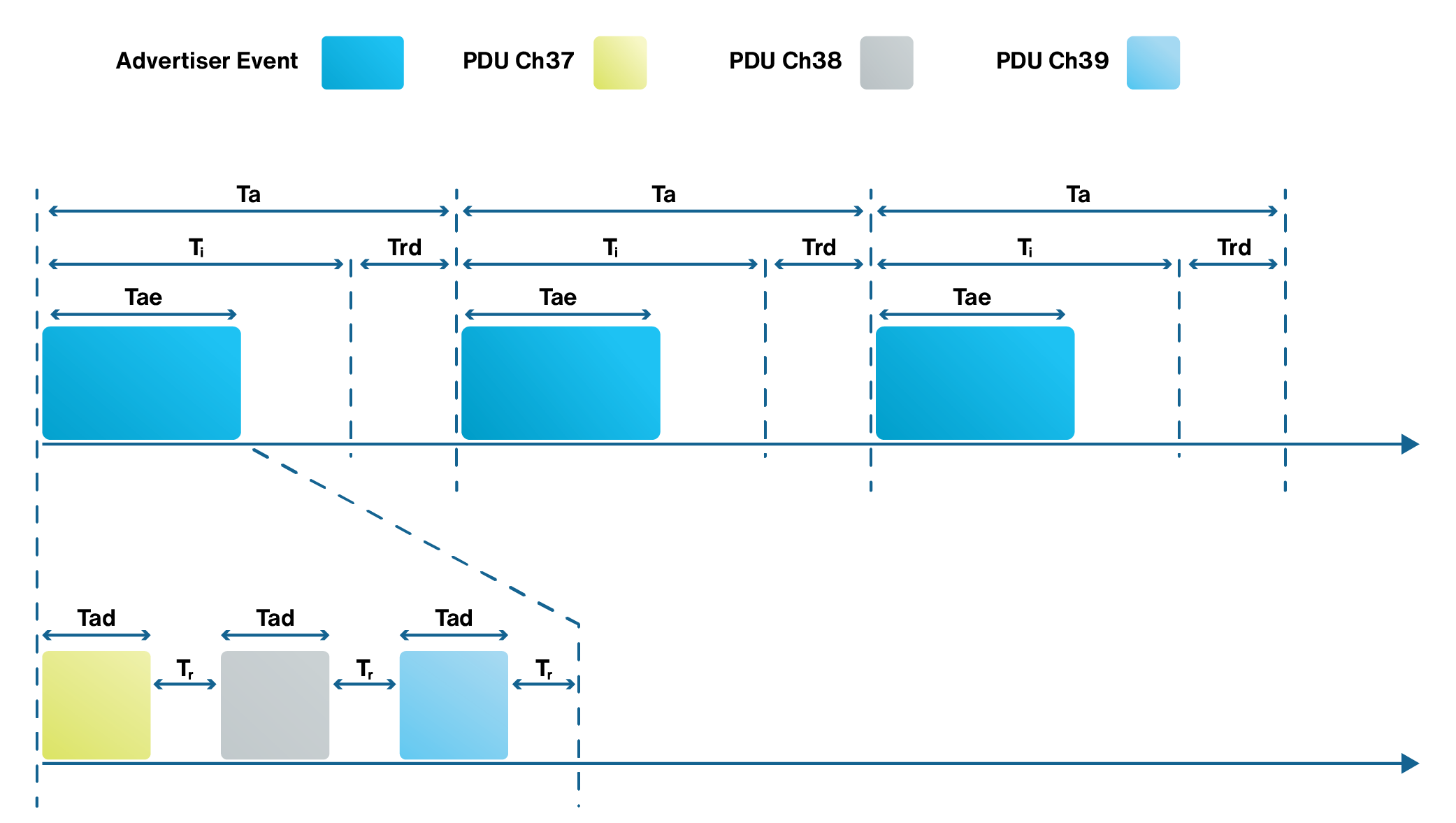
The advertiser periodically generates advertising events. Each advertising event consists of a sequence of advertising messages. Tad is the duration of time that will take for the advertiser to send an advertising message on a predefined advertising channel during each advertising event. At that time, the advertiser goes into the reception mode and listens for the duration of Tr on the same channel. Then, as shown in Figure A.2, the advertiser moves to the next advertising channel.
Two types of scanning are defined for a BLE device which are called passive scanning and active scanning. In passive scanning, a scanner receives advertisement messages, but does not send any packet to the advertiser, while in active scanning, the scanner listens to advertisement messages and after receiving an advertisement message, it sends a scan request packet to the advertiser. The scan request packet can help the scanner to learn more about the advertiser. For example, the scanner can ask about supported services by the advertiser. In response, the advertiser can send a list of its supported services.
The value of Tad is determined by the size of an advertising message. The size of each advertising message can be as small as 80 bits or as long as 376 bits. The value of Tr is adjusted to the tolerable time for the advertiser to wait for the scanner’s reply. The value of Ta represents the interval between two advertising events and consists of a fixed interval, Ti, and a variable interval which can be represented as a pseudorandom delay Trd . Based on BLE specifications, 20 ms ≤ Ti ≤ 10.24 s, 0 ≤ Trd ≤ 10 ms, and the value of Ti should be a multiple of 0.625 ms.
Since there is possibility of receiving several scan request messages from an advertiser by multiple scanners, it is likely that the packets collide with each other. If such a situation arose, each scanner should use a back-off strategy to minimize the possibility of collisions.
After receiving an advertising message by a scanner or initiator, they can initiate a connection. Connections enable a reliable communication for data transmission. To ensure robust delivery of data, Cyclic Redundancy Checks (CRC), acknowledgements, and retransmissions of lost or corrupted data are considered in BLE connections. BLE uses Adaptive Frequency Hopping (AFH) to detect and adapt hopping sequences dynamically to the surrounding environment and provide a robust physical layer. Data encryption is also supported by connections. A connection is initialized when a scanner (central BLE) sends a Connect Request packet. When the advertiser receives a Connect Request message and accepts this request, it stops advertising and follows the parameters in the Connect Request packet to start a connection. An advertiser checks several conditions before accepting the connection request. The advertiser needs to be enabled to accept connections and should not have any whitelist or if it has one, the initiator’s address should be in the whitelist. After establishing the connection, the initiator becomes the central node and the advertiser becomes the peripheral node. The central BLE node sends a connection event message on every connection interval. And the peripheral BLE node opens the scan window on every connection interval after the first connection event. The peripheral then sends a connection event packet toward the central node which acts as an acknowledgment. This packet may contain the user data as well.
The connection parameters provide information about the communication between the central and peripheral BLE node and are included in the Connect Request packet. A Connect Request packet contains several fields. The most important fields of this packet are interval, latency, and timeout. Connection Interval (CI) is the time between two BLE connection events. The peripheral BLE node specifies the minimum and maximum values of interval, but the CI value for communication is set by the central node when the BLE connection is first established. Some central BLE devices ignore the maximum and minimum values specified by the peripheral and use some default CI values instead. The duration of CI is equal to the interval times 1.25 ms. The BLE specifications state that the interval can be any value between 6 and 3200. In other words, the connection interval time can accept any value in the range of 7.5 ms to 4000 ms. Latency field defines the number of connection events the peripheral BLE node is allowed to skip the transmission. If the peripheral node does not have any data to send, it has the option to skip several connection events. This can provide some reduction in power consumption for the peripheral device. It should be noted that the peripheral BLE node should not stay too long in the sleep mode to lose its connection to the central BLE node. The number of consecutive connection events that the central BLE node continues its operation without receiving any data is defined as timeout.

