Chapter 4. Cloud Technologies
4.3 Site-to-Site VPN between Palo Alto on Premise and Palo Alto in the Azure
Learning Objectives
- Configure a Virtual Network in Microsoft Azure
- Set up and configure the Azure VPN Gateway for IPsec VPN
- Implement Network Security Groups (NSGs) in Azure for traffic control
- Monitor and troubleshoot IPsec VPN connections on Palo Alto
Scenario: In this lab, we will create a site-to-site VPN from Palo Alto on-premise to Palo Alto in the Azure. Knowing the configuration of section 4.2 is necessary for this lab. I have created management and ethernet1/1 as a DHCP, so they will receive an IP address from Cloud.
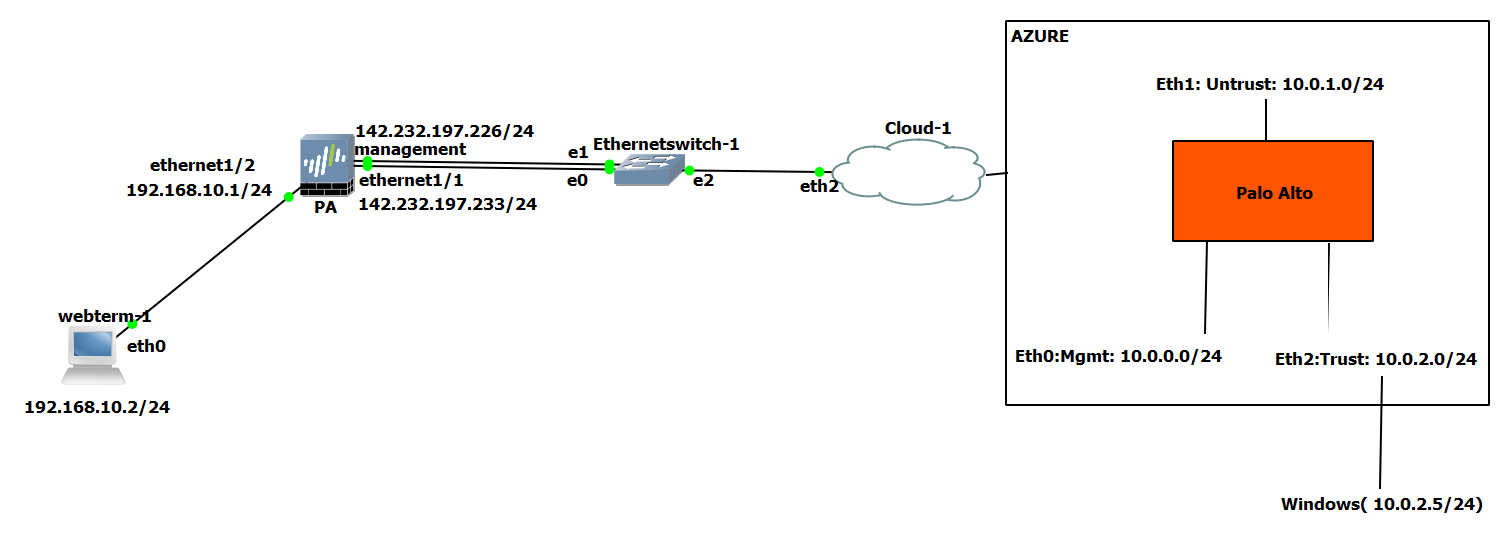
On-Premise Palo Alto Configuration
| Devices | Interface | IP address |
|---|---|---|
| Palo Alto | Management | DHCP Client |
| Ethernet 1/1 | DHCP Client | |
| Ethernet 1/2 | 192.168.10.1/24 | |
| WebTerm | Eth0 | 192.168.10.2/24 |
- Configure the interfaces of the firewall. Set Ethernet1/1 as a Untrust Zone and Ethernet1/2 as a Trust Zone.
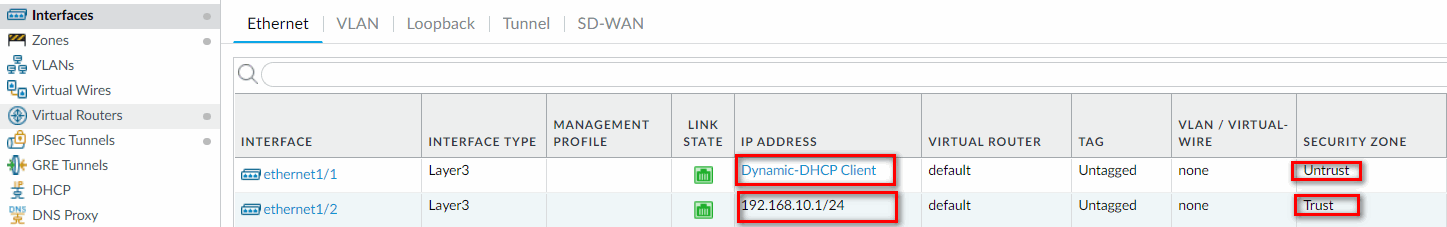
Figure 4.69: Firewall Interfaces - Create a tunnel.1 and set the tunnel as Untrust zone.
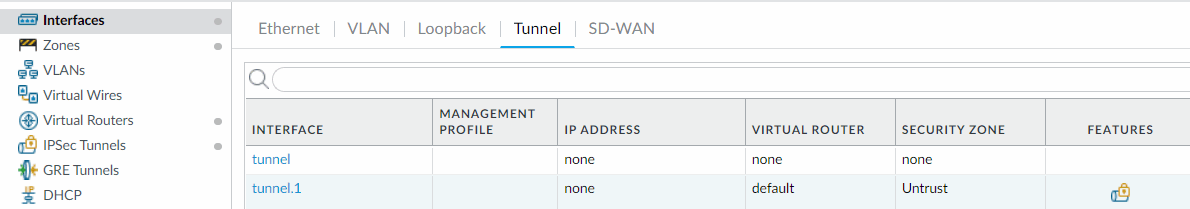
Figure 4.70: Create a tunnel - Create two static routes, one pointing to 142.232.197.254 (on-Prem Default Gateway) and the other one sending the traffic of Azure through the tunnel.
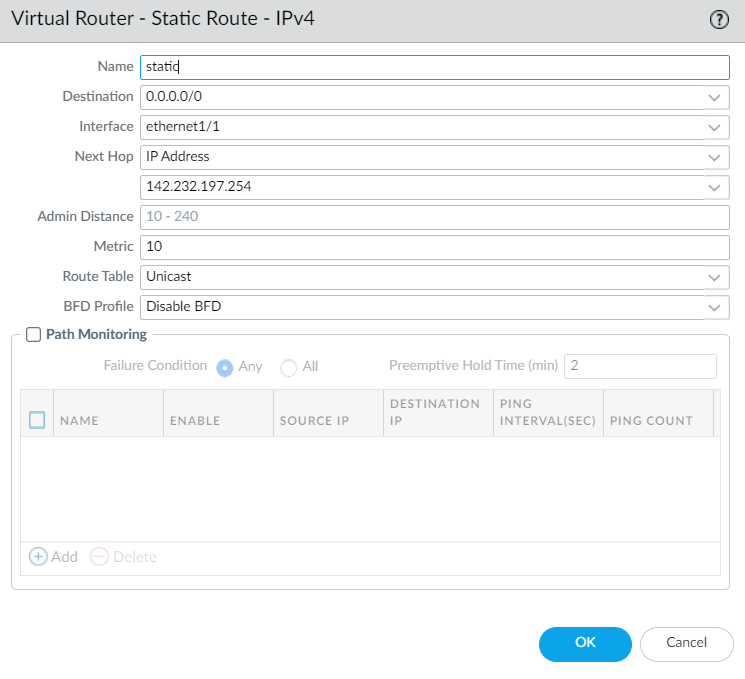
Figure 4.71: Create a static route to default gateway 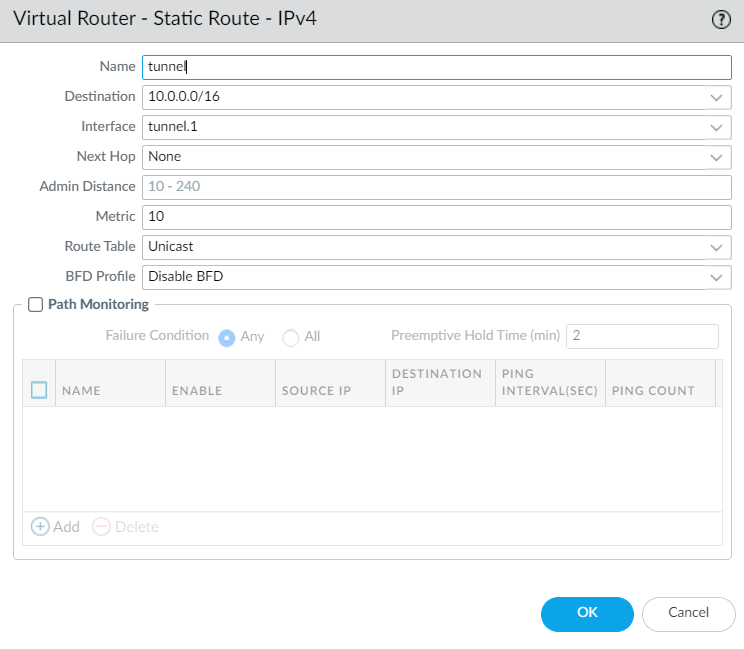
Figure 4.72: Create a static route to Azure - For setting up, site-to-site VPN we will use default IKE Crypto, IPsec Crypto profiles and we will only set IKE Gateway and IPsec Tunnel as following figures. You have to configure local and peer identification.
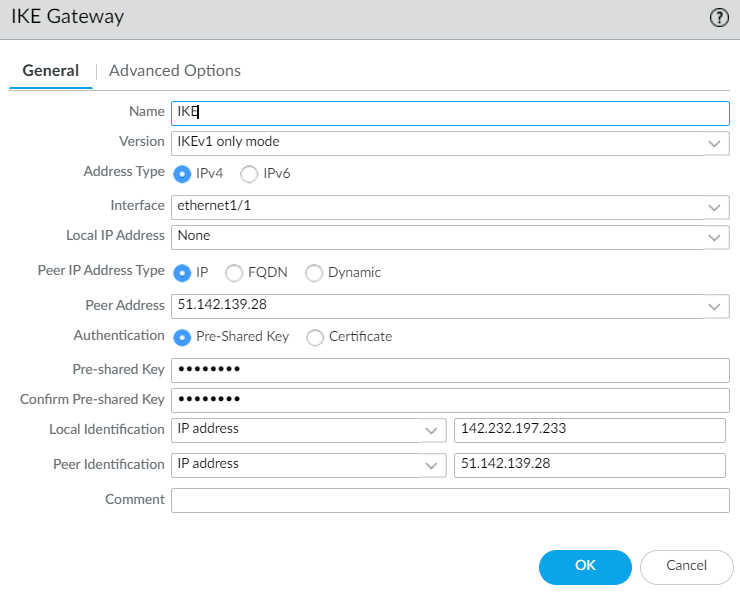
Figure 4.73: Create an IKE Gateway 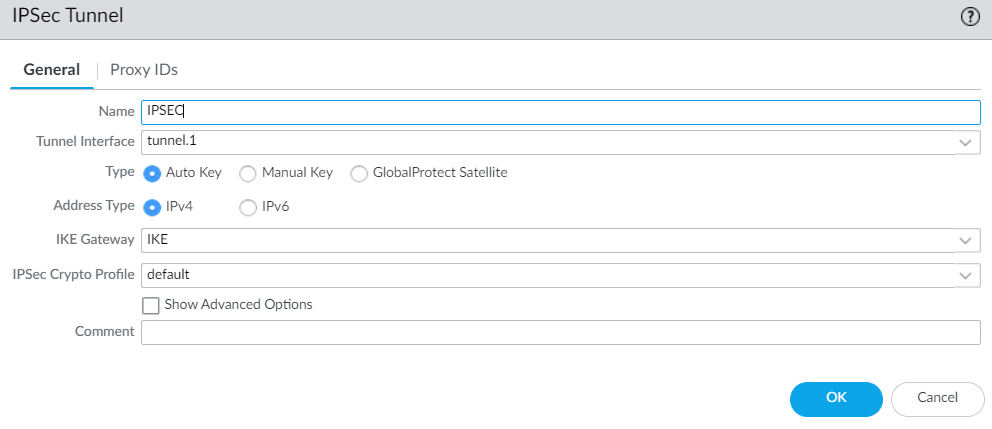
Figure 4.74: Create an IPsec Tunnel - Finally, create two security policies, one from Trust to Untrust zone and the other from Untrust to Trust zone.
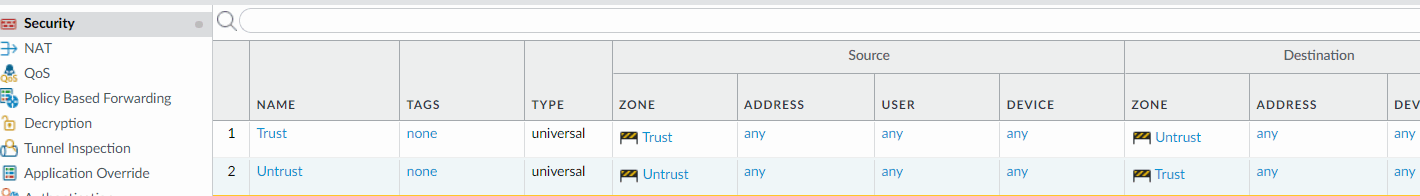
Figure 4.75: Create two security policies
Azure Configuration
- Create a Palo Alto firewall in Azure and configure the interfaces. You need to do all steps in section 4.1 and assign public IP address to Ethernet 1 (Untrust Zone).
- Create a route in Azure pointing to Trust interface.
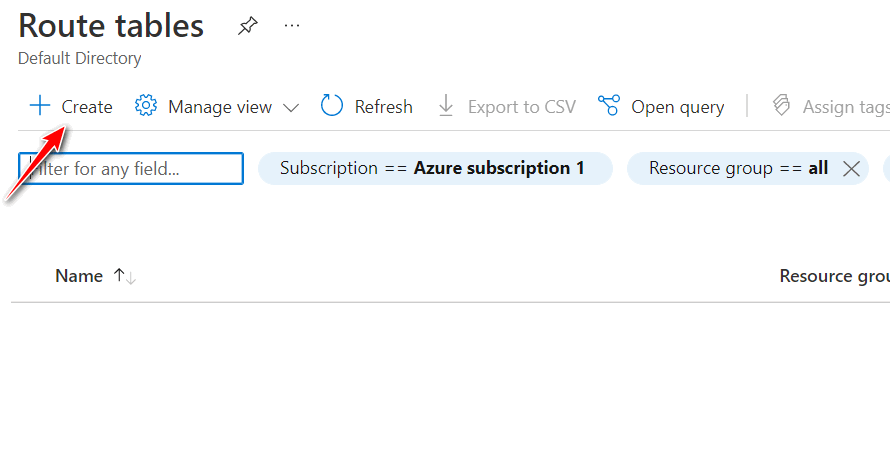
Figure 4.76: Create a route table 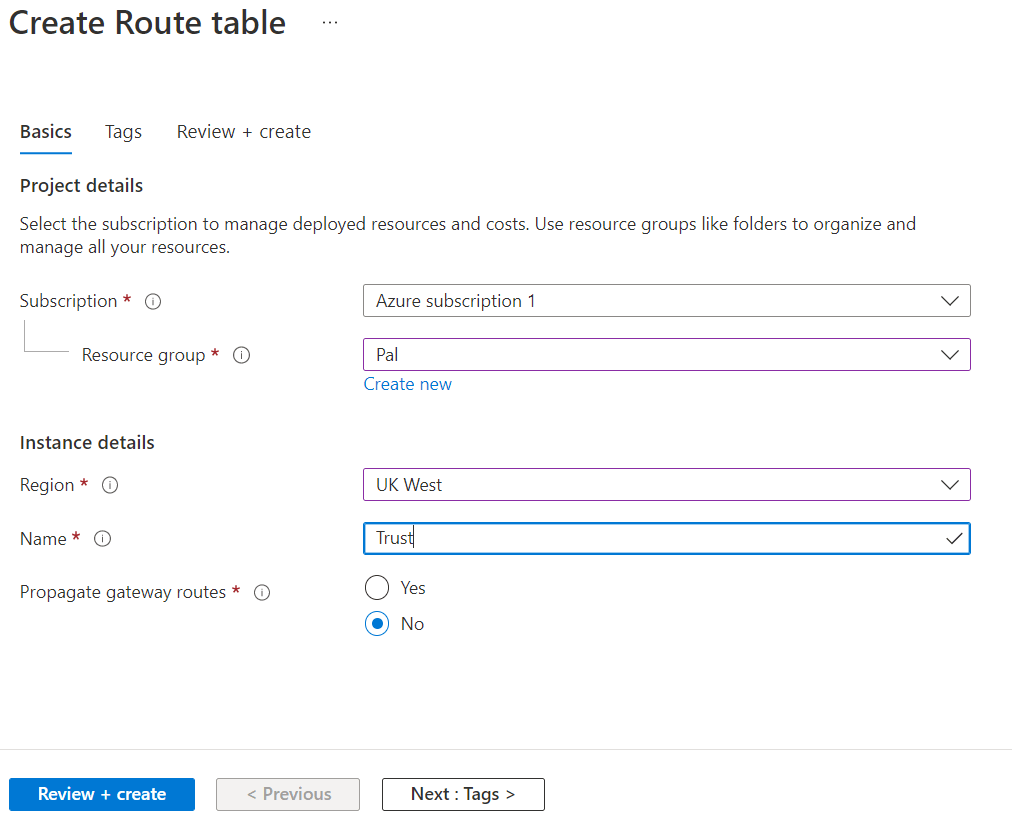
Figure 4.77: Create a route table 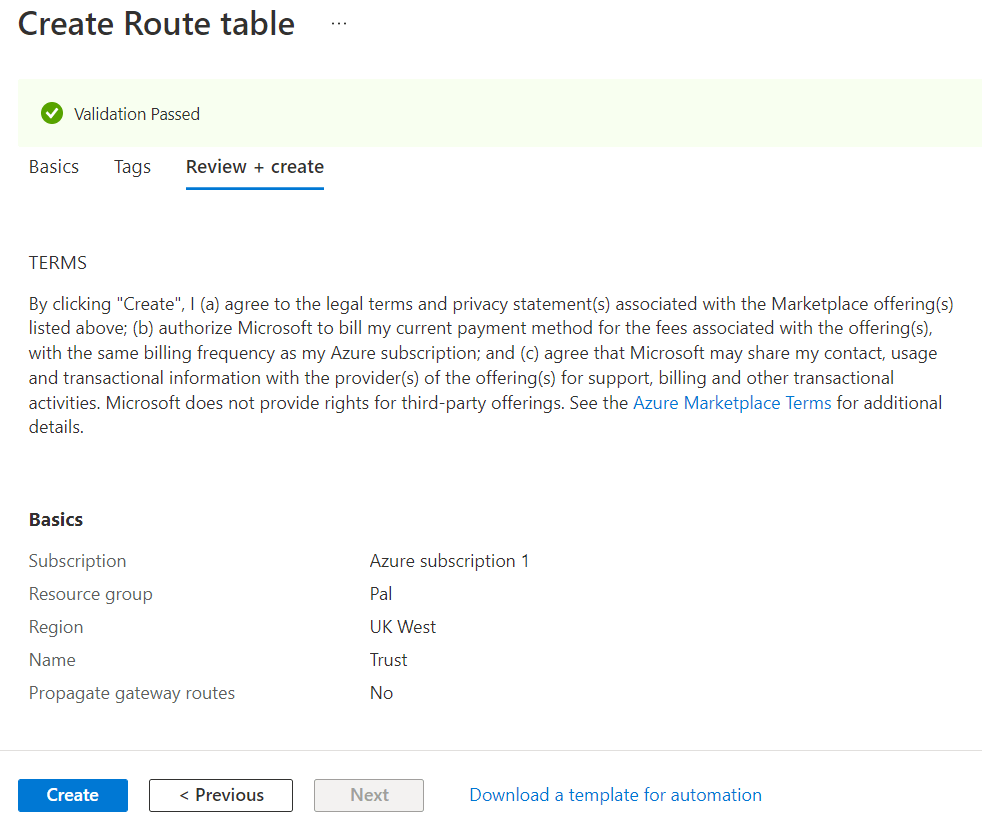
Figure 4.78: Create a route table (verify and create) 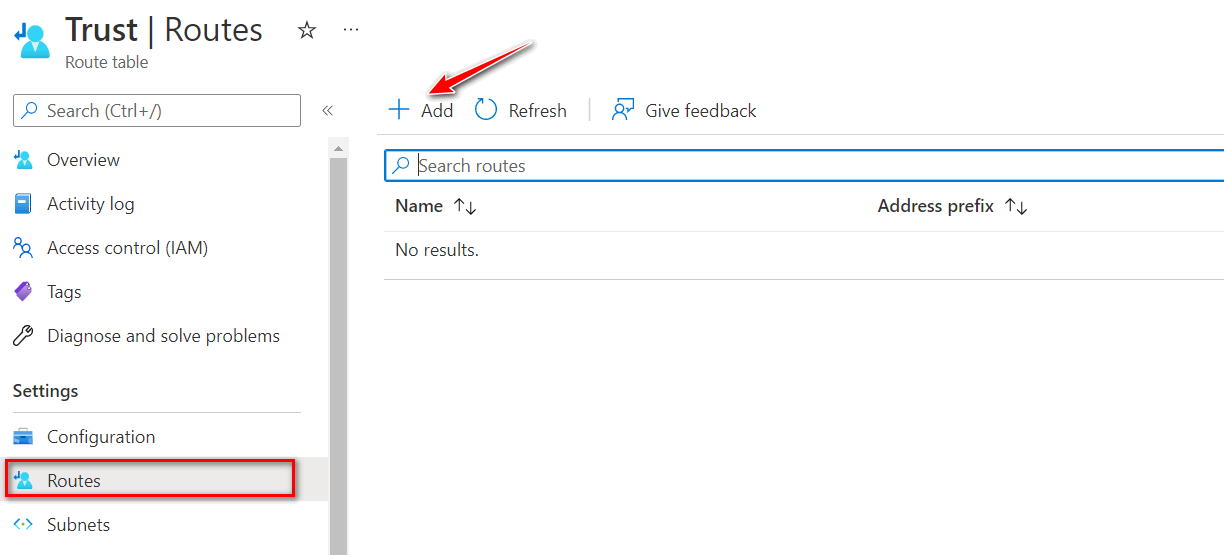
Figure 4.79: Add a Route 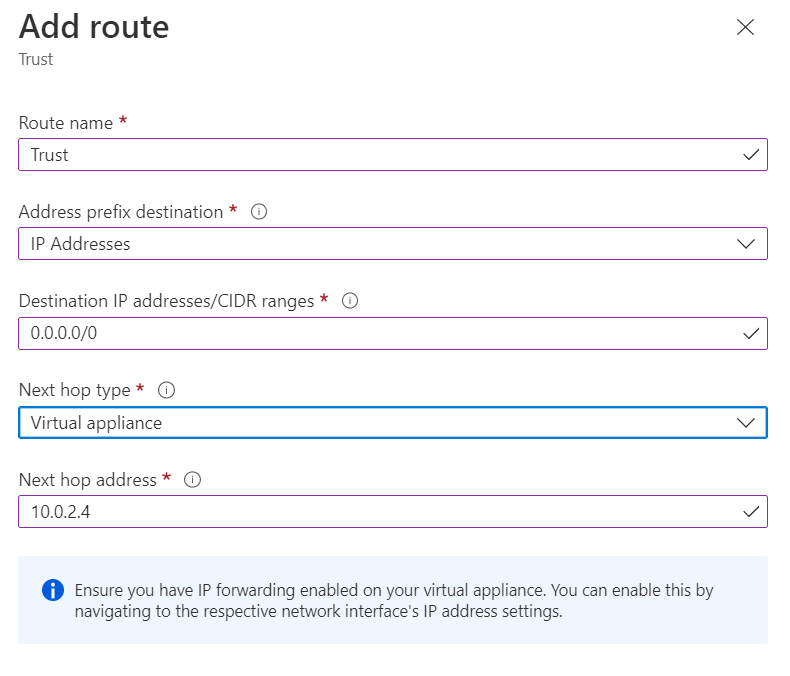
Figure 4.80: Add a default route pointing to 10.0.2.4 (Trust Interface) 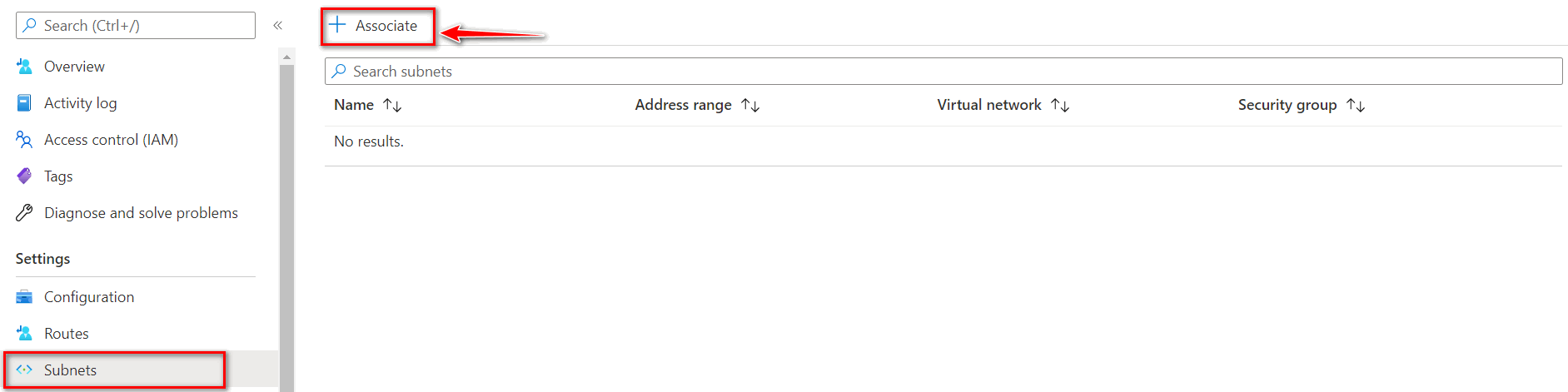
Figure 4.81: Associate Trust route to Trust Subnet 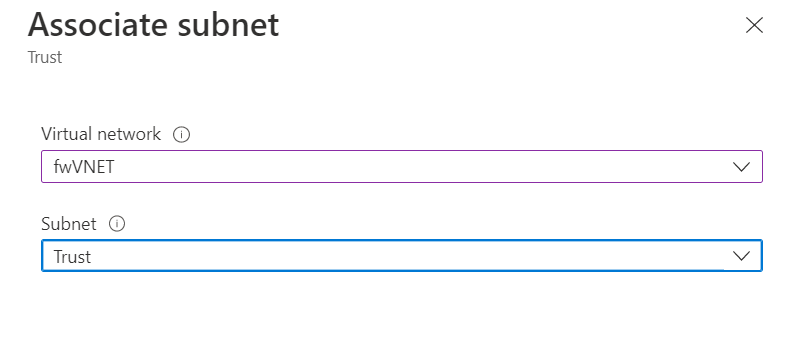
Figure 4.82: Associate fwVNET to Trust Subnet - Set static routes as figures 4.83 and 4.84.
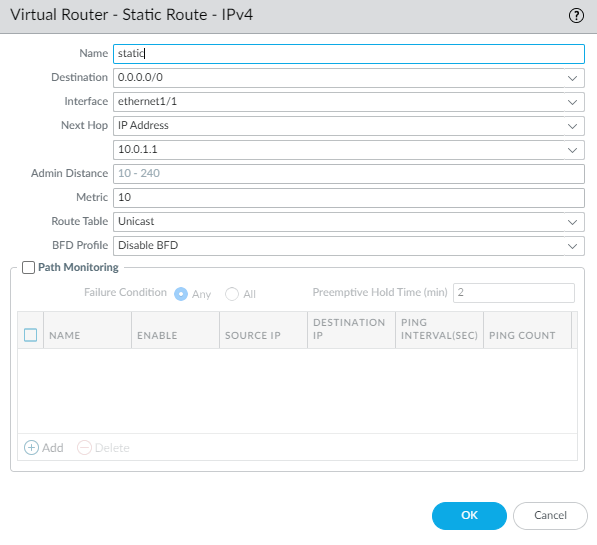
Figure 4.83: Static route pointing to default gateway 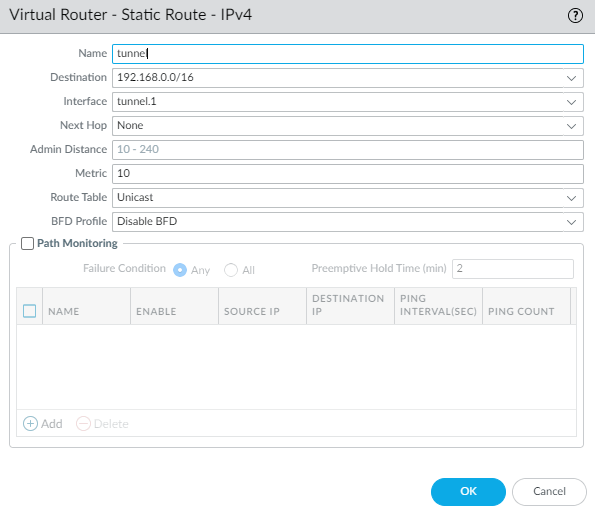
Figure 4.84: Static route pointing to tunnel - For setting up, site-to-site VPN we will use default IKE Crypto, IPsec Crypto profiles and we will only set IKE Gateway and IPsec Tunnel as figures 4.85 and 4.86.
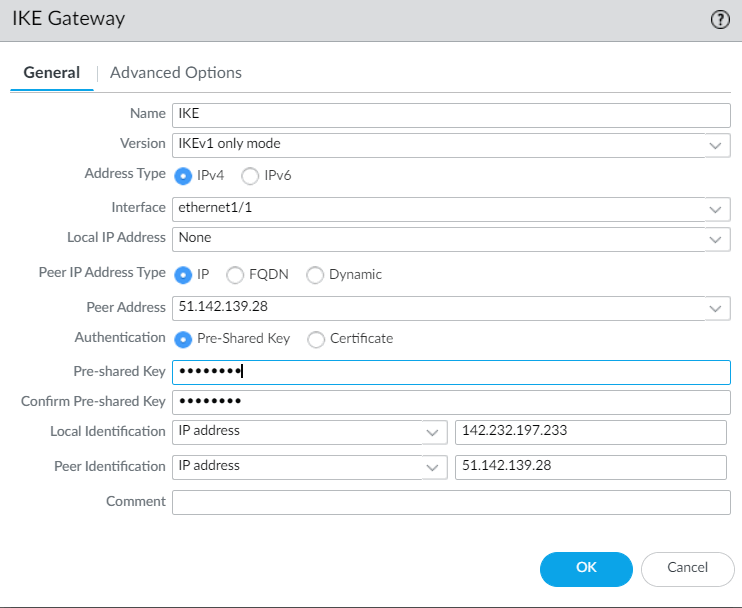
Figure 4.85: Create an IKE Gateway 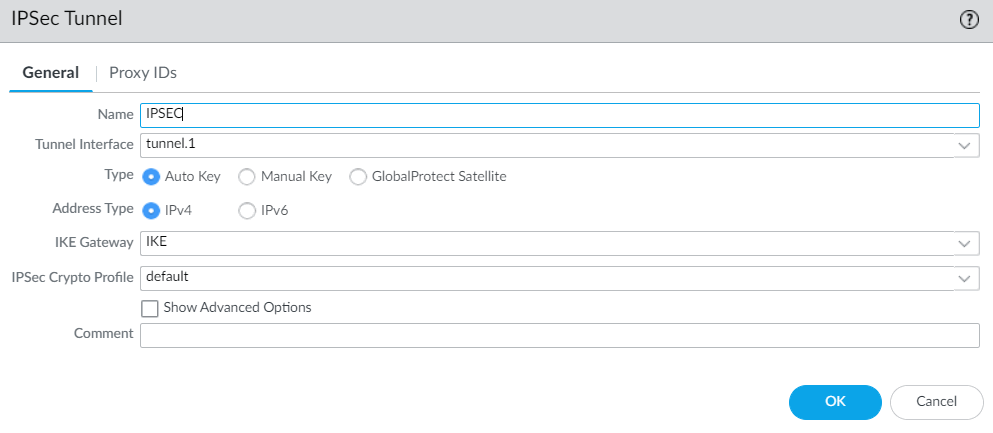
Figure 4.86: Create an IPsec Tunnel - Finally, create two security policies, one from Trust to Untrust zone and the other from Untrust to Trust zone.
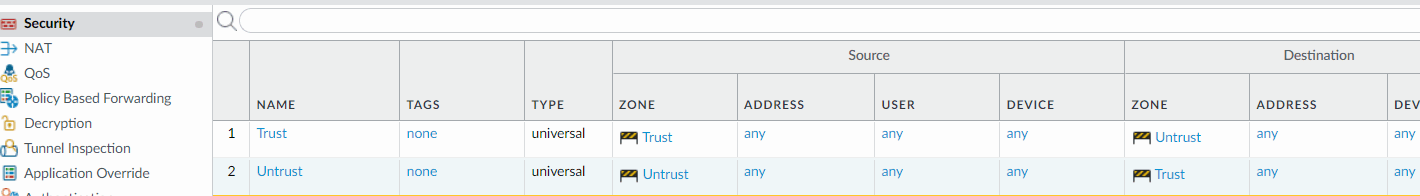
Figure 4.87: Create two security policies - Add windows or Linux VM to Trust Subnet. This VM is for testing ping from Azure side to on-prem. We will not create a public IP address for the VM.
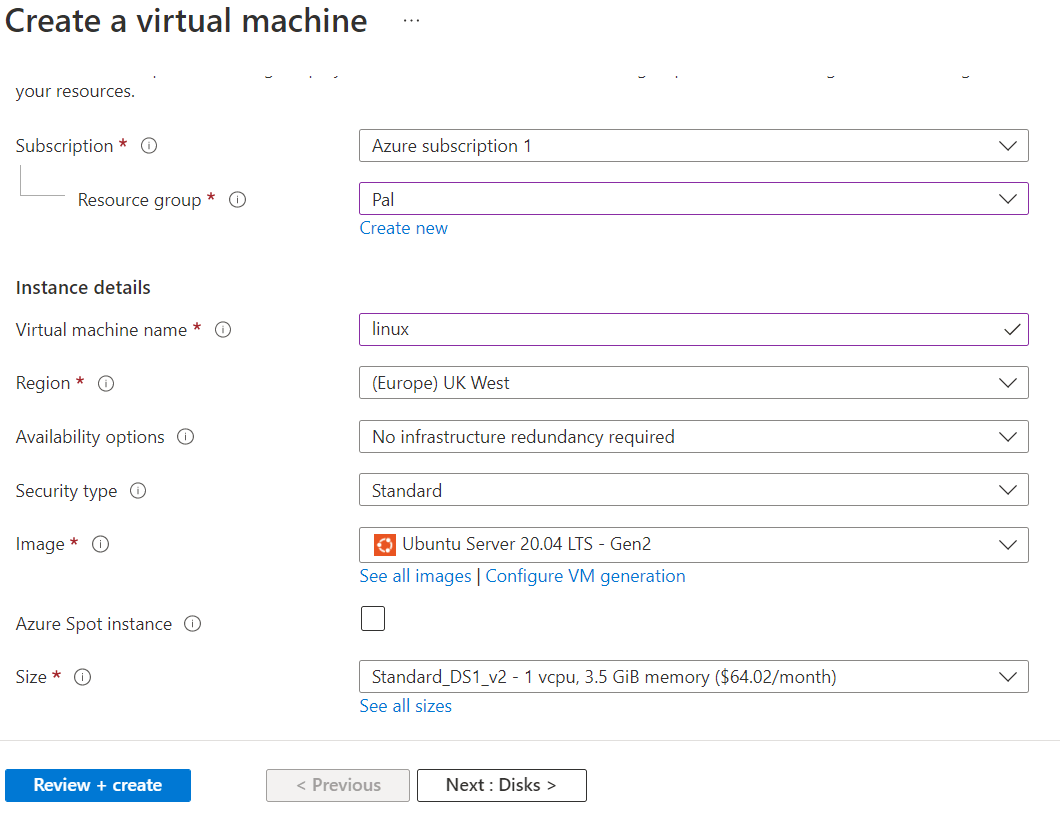
Figure 4.88: Create a VM 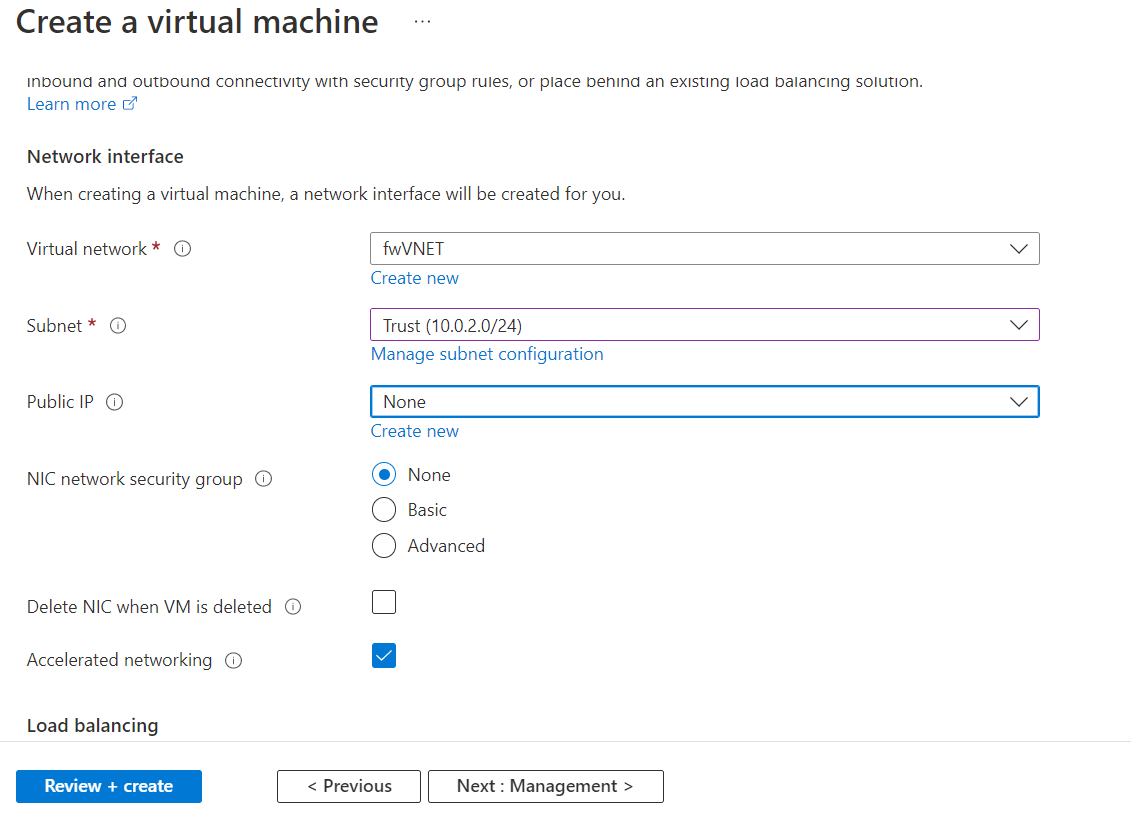
Figure 4.89: Assign Trust subnet with no public IP - Now, you should be able to ping and your tunnel should be green.
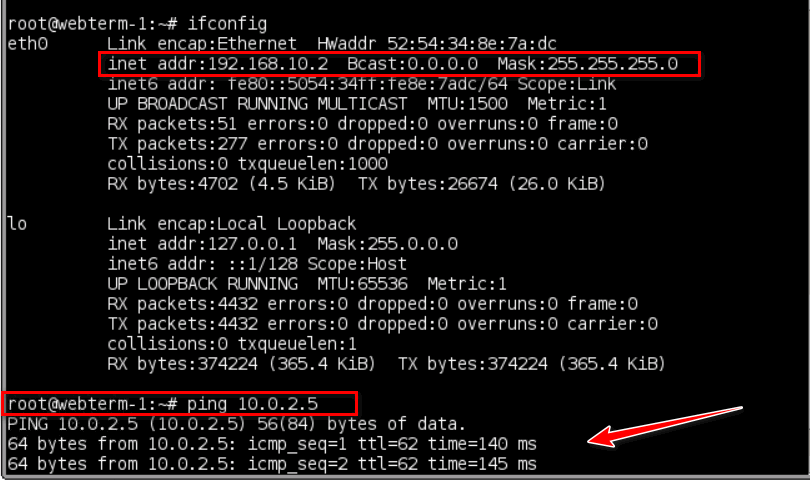
Figure 4.90: Ping from WebTerm to Azure 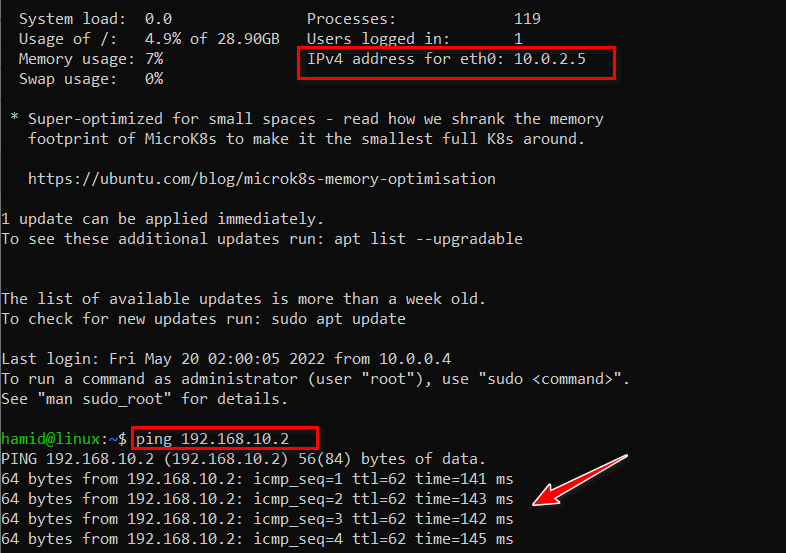
Figure 4.91: Ping from Azure to WebTerm 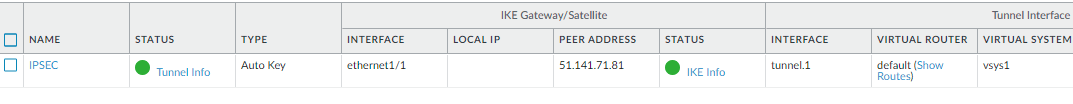
Figure 4.92: Tunnel Status

